5 min read
Ransomware is a popular weapon for cyber criminals. Worldwide in 2020, there were 304 million ransomware attacks, a 62% increase from the year prior, according to Statista. All verticals are vulnerable to these ransomware attacks, which if successful, are a blot on financial statements of the targeted organizations. The success of these attacks underscore poor endpoint protection plans and strategies that befall companies of every size and every vertical. This leads to most organizations reacting to ransomware rather than planning against it, which is expensive in staff hours and of course hurtful to reputation.
Ransomware attacks have disrupted organizations around the world, from hospitals across Ireland, Germany and France, to pipelines in the United States and banks in the U.K. The threats are serious, and they are increasing
– White House memo in 2021 on cybersecurity
Here are five common misconceptions about ransomware. Read on to learn how ransomware works, ways to detect it, and how to mitigate it.
Myth #1: Ransomware is a Zero-day attack.
In fact, exploiting a Zero-day vulnerability is an expensive proposition for a malicious actor. In reality, most malware targets known vulnerabilities, which while well-documented and easily remediated, remain unpatched. Therefore, a systematic schedule of patching and endpoint system updates within 30 days of becoming available is the most effective way to minimize the threat of ransomware, and indeed most “targeted” attacks.
Myth #2: Anti-virus and perimeter solutions are sufficient protection.
Signature-based protection has been widely used for 20+ years and is a necessary and effective protection mechanism. However, this approach is well known and easily evaded by attackers. In addition to signature-based anti-virus solutions, it is necessary to consider Endpoint Detection and Response solutions supported by monitoring and analytics.
Myth #3: Flat networks make an ideal architecture.
Many ransomware attacks are successful because attackers breach perimeter security solutions and web-facing applications. Most networks are flat or unsegmented, making them easy for attackers to gain broad organizational access. Segmenting network assets into trust zones and enforcing traffic flow rules is the way to go. Unlike a flat network, a segmented network limits the blast radius and impact of a potential data breach. Limiting risk and exposure is just one step in ensuring business resilience.
Myth #4: IT admins always follow best practices.
When administrator accounts are not properly monitored, it exposes super users to hacker opportunism. High priority target accounts include System Admin workstations with drive mappings and often used (and sadly common) administrator passwords to critical servers. Monitoring administrator accounts for unauthorized use, access, and behaviors is a cybersecurity best practice in frameworks such as the NIST Risk Management Framework (RMF).
Myth #5: Ransomware is all about tools and technology.
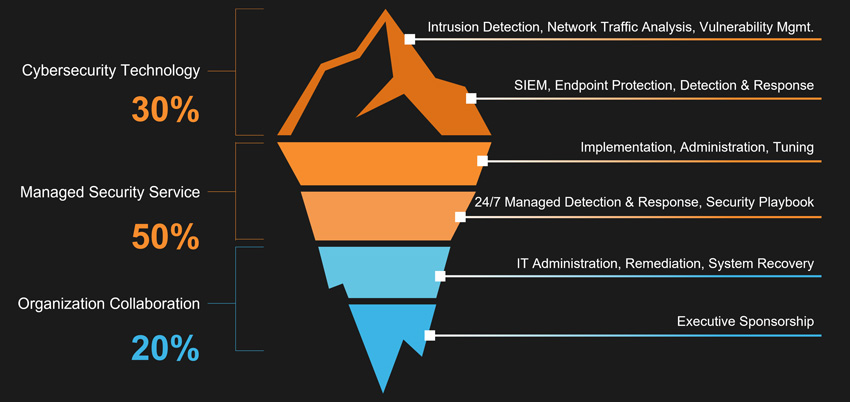
While critical products like SIEM and Endpoint Protection Platforms improve ransomware defense, tools alone are not sufficient against today’s evolving cyber criminals. As the figure below highlights, technology is just the tip of the iceberg in threat mitigation. Cybersecurity and ransomware are a people issue, from social engineering and insider threats to configuration errors that create security gaps. The right combination of people, process, and technology is essential given the ever-rising threat of ransomware and business exploitation. With over 3 million unfilled cybersecurity jobs, look to proven service providers for security expertise as a necessary boost to your staff and skill set.
Take the Next Step
Ransomware variants and criminal gangs show no signs of slowing down. Attackers have been quick to shift their techniques to take advantage of configuration mistakes and endpoint gaps. Minimize ransomware risk and expense with a proactive and practical approach to cybersecurity. With Netsurion’s Managed Threat Protection, rapid detection and response elevates your security posture and can mean the difference in 206 days detection to closer to real-time prevention. Learn more about our complete managed security platform to predict, prevent, detect, and respond to threats across your entire organization.

Paula Rhea
Paula Rhea, CISSP is a product marketing manager at Netsurion. She is responsible for developing go-to-market strategies for customers and partners regarding managed threat protection and secure edge networking. Paula has extensive cybersecurity experience in managed services, compliance, and endpoint protection.

