Welcome to “Ransomware Deconstructed,” an in-depth video series that peels back the layers of one of the most pervasive cyber threats of our time. In this miniseries, we embark on a journey to demystify ransomware by addressing key questions. Join us as we explore why ransomware has exploded and provide you with valuable insights to safeguard your digital assets and navigate the evolving cyber threat landscape.
Introduction to Ransomware Deconstructed

Netsurion’s Chief Strategy Officer and co-creator of our Open XDR platform, A.N. Ananth, provides expert insight into the topic of ransomware. Topics in this Ransomware Deconstructed video series include: what is ransomware and why has it exploded in recent years, what is the lifecycle of a ransomware attack, types of prevalent ransomware, who is attacking, and more. Join us and uncover details about ransomware.
Why has ransomware exploded?
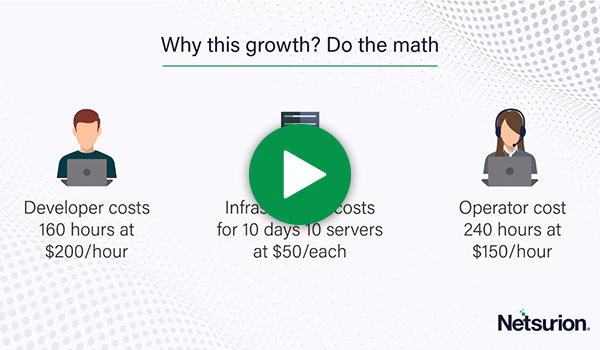
Ransomware has been around in some form or fashion for more than three decades but only recently became prevalent in terms of widespread cybercrime usage. Ransomware alone makes up nearly a quarter of all malware incidents. So, what’s the cause for the increased popularity of ransomware? Watch this short video to find out the simple answer.
What is the lifecycle of a ransomware incident?
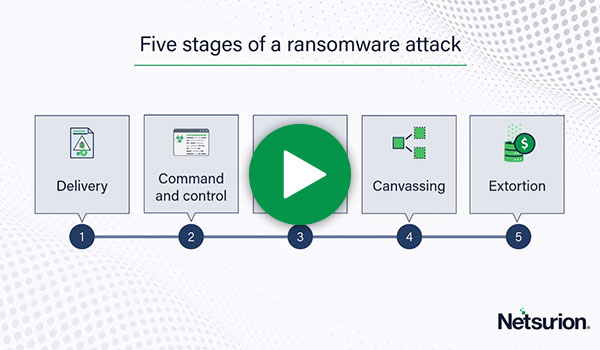
Understanding the stages of a ransomware attack is key to knowing how to defend against it. Watch this video to review the lifecycle of ransomware incidents from target identification to encoding/encryption of your environment so you are better prepared for detection and quick response in the event your organization becomes a target.
What types of ransomware are prevalent?
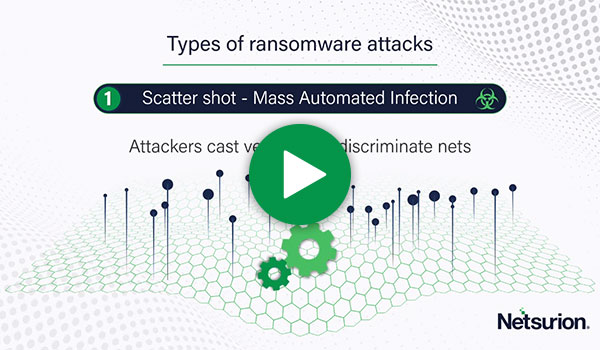
Multitudes of ransomware packages are available for those with malicious intent who wish to search them out and find them. However, types of ransomware can really be broken down into 3 broad categories in use today. Check out this video to learn what these three categories are and how each works so you can be better prepared in the event of an incident.
Who attacks using ransomware?

Who attacks using ransomware? The easy answer is a hacker of course. In the past, threat actors tended to be part of either a criminal gang or a state-sponsored group. However, a third type of threat actor has emerged that is more business-minded and risk-averse than their predecessors. Check out this video to find out the answer to who attacks using ransomware.
What policies are used in responding to ransomware?
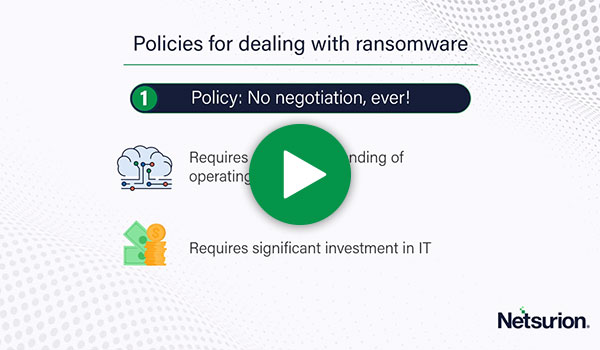
There are differing mindsets when it comes to responding to a ransomware incident. Some take a hard-nosed approach and refuse to pay out in the event of a ransomware incident. Others may be more willing to negotiate in certain circumstances. Each organization and levels of security will differ, so there isn’t a blanket policy across the board. Check out this video for ideas on what must be in place for each type of response to ransomware.
What are the key roles in responding to ransomware?
In the event of a ransomware incident, does your organization have the people in place to fill the key roles needed? This is not just an IT effort, it requires incident response, legal minds, public relations, cyber insurance providers, and more. This video is a must-watch if you’re unsure you have the policies and staff in place to tackle ransomware.
What constitutes an effective defense against ransomware?
Now that we’ve reviewed the ins and outs of ransomware, it’s time to ensure you’re defended in the event of an incident. Unfortunately, there’s not a silver bullet solution that alone covers you against ransomware attacks. However, a proactive and layered approach to security will limit the chances of an event occurring. Check out this video to learn more about defense-in-depth coverage for your organization.