Threats are dynamic and attack vectors change constantly. Detect threats quickly and minimize damage with rich context enabled by threat intelligence and Indicators of Compromise (IoCs).
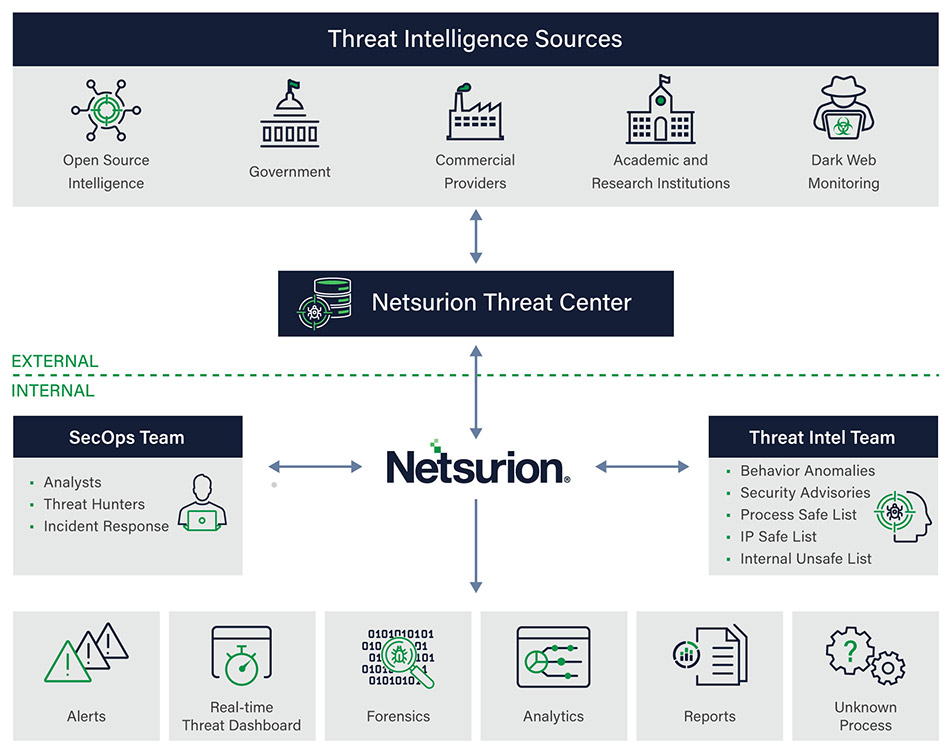
Netsurion Threat Center, our threat intelligence platform, incorporates threat intelligence from various providers, including global open source feeds, those curated by the threat team at Netsurion, and contributions from the Netsurion community. This data can then be leveraged to reduce false positives, detect hidden threats, and prioritize your most concerning alarms. The Netsurion console ingests these consolidated feeds from Netsurion Threat Center and can combine them with commercial feeds subscribed to by the customer as well as rules specific to the installation. These consolidated feeds provide the optimum mix of threat intelligence: global, community, and local.
* Threat feeds are constantly evaluated for effectiveness and may be adjusted.
Correlate Global Threat Feeds for Greater Effectiveness and Coverage
Global threat feeds are correlated for greater effectiveness and coverage. Local or community information augment comprehensive global feed data to provide optimum coverage. Netsurion Threat Center combines that data with insights from internal sources such as:
- Process safelists
- IP internal safelists
- Internal unsafelists
- Contributions from Netsurion SOC analysts
Embedded Threat Intelligence
Netsurion Threat Center provides additional context and correlation between seemingly unrelated security events, resulting in faster identification of Indicators of Attack (IoAs). Netsurion ingests over 30 open-source intelligence (OSINT) feeds and uses the STIX/TAXII framework to automate the process of threat detection, analysis, and response.
Netsurion Threat Center continuously imports up-to-date information about top attackers, spammers, poisoned URLs and malware domains from a variety of threat feeds such as EmergingThreats.net, IPReputation.com, IPVoid.com, the NSRL and SANS. These threat sources contain:
- Known Command and Control (C&C) hosts
- Attack response rules
- Compromised hosts
- Systems of known spammers
- Rules for detecting exploits, SQL injection, etc.
- User-Agent strings for known malware
- Web server attack detection rules
Netsurion Threat Intelligence Enhances Current Threat Detection

Improving alerting and elevating the priority of rules that reference IoCs determined by shared threat intelligence.
Automatic notification of external IP addresses communicating with assets behind your firewall.
Detection of compromised systems that attempt to connect externally from inside your network.
Historic IP address retention based on collected threat intelligence data for additional context.
Correlation of the presence of IoC everywhere within your network for comprehensive remedial action.
Threat Center Helps Detect Dharma Ransomware
Find out how security analysts utilize our threat intelligence to keep partners and customers safe from advanced threats. View how a Netsurion MSP partner utilized our Open XDR platform and Threat Center intelligence to detect ransomware that was found in their end customer’s environment.
