Detect Threats Earlier with Behavior Analytics
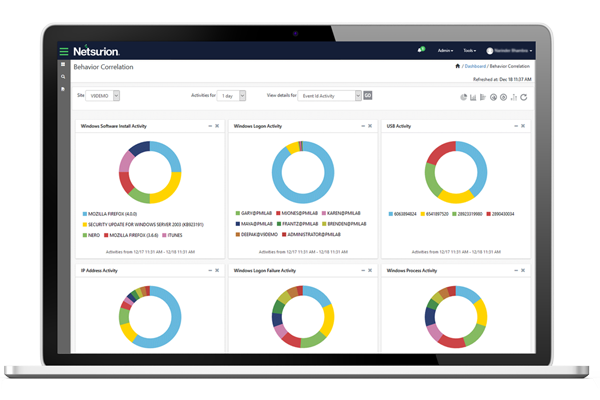
Netsurion’s User & Entity Behavior Analytics (UEBA) capability uses Machine Learning (ML) to understand how users (humans) and entities (machines) typically behave within an environment, then to find risky, anomalous activity that deviates from their normal behavior, and then alert to a potential threat. Examples of UEBA use cases include:
- Identifying a user accessing a system at an unusual time or location
- Detecting a user accessing a system not in their standard routine
- Finding an entry point where a user or device has attempted to log into various sensitive assets or locations
All this analysis, correlation, and reporting is done by collecting and storing telemetry and log data within our SIEM (Security Information and Event Management) technology. Netsurion incorporates UEBA to detect risk early and limit damage.
Threats Inside are Challenging to Find and Eradicate
Insiders know where all the sensitive data is located and how to exploit security gaps. Human error also creates risk. Types of insider threats include:
- Inadvertent insider threats
- Malicious insider threats
- Attackers who get into your network and masquerade as employees or supply-chain partners
- Faster detection means less damage and need for remediation

Detect Lateral Movement Early to Minimize Damage
Attackers use stealthy tactics like lateral movement to gain access to your network and pivot to other more valuable data to steal or ransom. It is difficult to uncover lateral movement on your own due to alert fatigue and criminals masquerading as sysadmins. Alert fatigue makes it difficult to uncover lateral movement on your own. Netsurion builds in UEBA to create a baseline of standard behavior and then quickly detects suspicious behavior that mitigates threats early. Our knowledge of your infrastructure and SecOps helps uncover attacks in progress and protects sensitive data before it can be exfiltrated.
Automate a Rapid Response to Boost Resiliency
Deter cyber criminals and stop malicious insiders, privilege abuse, compromised login credentials, and data theft with UEBA and a 24/7 Security Operations Center (SOC). Netsurion’s open XDR platform incorporates behavioral analytics, response automation and orchestration, and an intelligence-driven SOC to achieve cybersecurity confidence and control. Behavior Analytics enables you to prioritize and focus limited resources on the highest severity and risky scenarios by providing threat intelligence context and pinpointing areas for preventive action.

Talk to a Cybersecurity Advisor
Looking to optimize your cybersecurity posture with Managed XDR? Choosing the right partner is crucial. Talk to a Cybersecurity Advisor to see if we’re a fit.