Managed Open XDR
Cybersecurity is an arms race in which hackers find new ways to attack and defenders struggle to keep up. Netsurion’s defense-in-depth approach ensures that you have the people, process, and technology to future-proof your security without breaking the bank. Netsurion’s cloud platform drives security operations so that any threat intelligence and adversary insights are leveraged across our entire customer community.
End-to-End Managed Threat Protection
Comprehensive cybersecurity requires the ability to predict and prevent more threats before they occur, and detect and respond to attacks immediately.
Pre-Breach
Predict
Understand your attack surface and efficiently manage vulnerabilities.
Prevent
Stop more ransomware and malware attacks before they execute.
BREACH
Post-Breach
Detect
Catch suspicious behavior and correlate advanced attacker techniques.
Respond
Resolve security incidents and compliance issues quickly and completely.

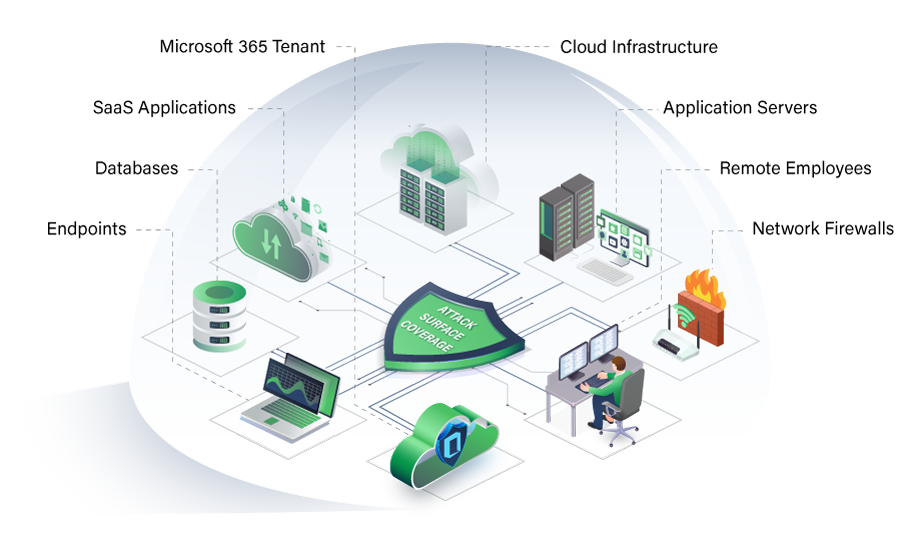
Wider Attack Surface Coverage
Your business has many points of cyber-attack vulnerability.
Your IT attack surface is constantly changing and growing. Remote employees, cloud infrastructure, and an increased reliance on SaaS applications help organizations remain flexible, but also introduce vulnerable points of entry. To confidently defend yourself from cyber attacks like ransomware and zero-day exploits, ensure all vulnerable access points are protected with complete attack surface coverage.
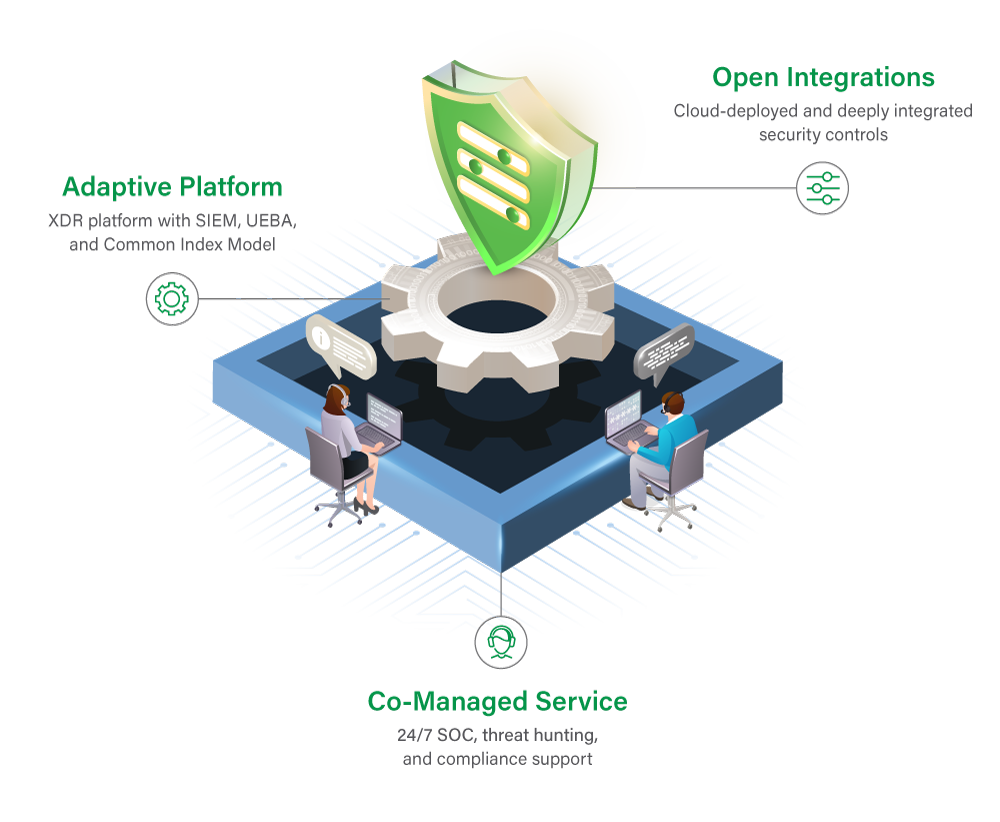
Future-Proofed Cybersecurity
We future-proof your cybersecurity with our unique co-managed approach that includes a powerful XDR platform architecture, a wide array of extensible controls and automations, and all driven by a fully-staffed 24×7 SOC.
What Keeps You Up at Night?
View our solution by what environments you struggle to defend, what industry regulations you need to comply with, or by what threat type you’re most worried about.
Talk to a Cybersecurity Advisor
Looking to optimize your cybersecurity posture with Managed XDR? Choosing the right partner is crucial. Talk to a Cybersecurity Advisor to see if we’re a fit.