4 min read
Threats and threat actors continue to evolve and morph, creating advanced and even more dangerous tactics to mitigate. October is National Cybersecurity Awareness Month (NCSAM). NSCAM 2019 centers on the theme of Own IT. Secure IT. Protect IT., advocating a proactive approach to enhanced cybersecurity in the workplace and at home.
Your online web presence is the crown jewel of your business or government organization. Your website conveys your brand to prospective customers and often facilitates e-commerce and citizen services. It is also a doorway into your business, servers, and valuable financial data, as well as links you to a global supply chain network. Good website security is vital for data protection and even disaster recovery and resiliency.
Facts to Know
- 49% of small businesses have experienced a web-based attacks
- Over 75% of cybersecurity attacks are financially motivated, according to the 2019 Verizon Data Breach Investigation Report
- If a company has a password policy, 65% of small businesses say they do not enforce it
- Ransomware volume is up 50% globally in 2019, according to the Identify Theft Resource Center
Impacts and Motivations of Website Attacks Threats and attacks against your website or portal can lead to reduced revenue, dissatisfied visitors, compliance fines, and a lack of trust by valuable customers, e-commerce buyers, and business partners. Hackers have a wide range of motivations for website attacks:
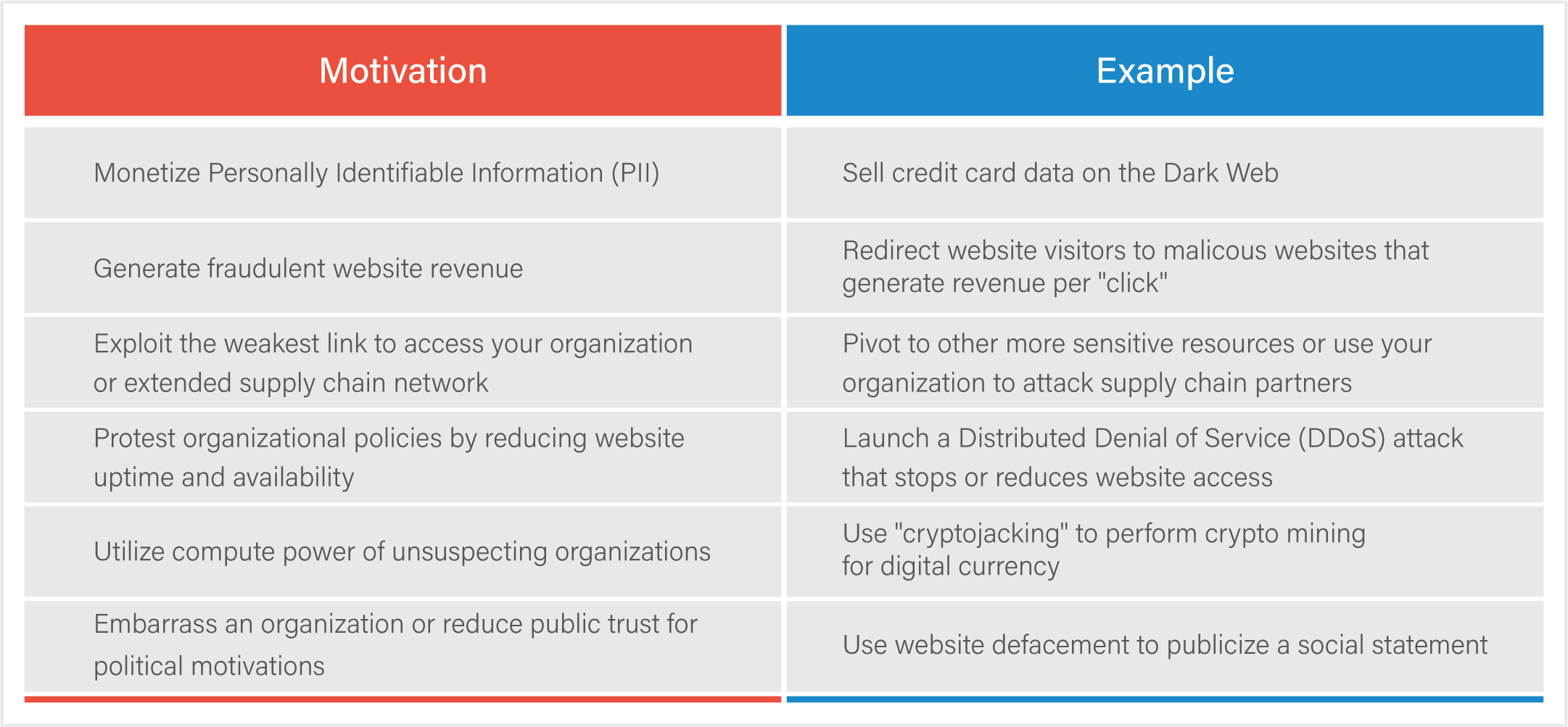
Regardless of the hacker’s initial motivation, website threats are real and require a range of countermeasures to deter these attacks. Build cybersecurity into your site technology and staff practices from the start, don’t bolt it on after it’s too late.
Simple Website Protection Steps to Own IT. Secure IT. Protect IT.
Use authentication best practices. Eliminate credential compromise and account takeover by requiring strong passwords, implementing role-based access controls (RBAC), and eliminating logins immediately for departing employees and vendors. System admins with their privileged access to data centers and servers are especially targeted. Don’t make it easy for hackers to buy and sell your organization’s logins on criminal forums.
Disable unnecessary accounts and web plug-ins. You can’t manage and patch assets that are long forgotten and sitting unused. Hacker tactics, techniques, and procedures (TTPs) actively exploit legacy applications and systems with known security gaps that provide low hanging fruit to attack.
Implement regular vulnerability assessments. Avoid website attacks by identifying vulnerabilities, malware, and configuration gaps that leave you exposed. Think like a hacker with a systematic approach to vulnerability scanning and remediation.
Maintain good cyber hygiene. Don’t forget cybersecurity basics that are low hanging fruit for attackers: use network segmentation to partition your network to limit the “blast radius” and ease restoration after a cyber attack. Avoid vendor default settings that represent the first path that threat actors will attempt. Rapidly apply security patches when they are released, especially for website software and tools.
Automate data backups. Ensure regular data backups and store them separately from your operating network and servers. A robust backup strategy is crucial for data security as well as disaster recovery and continuity requirements for frameworks such as PCI DSS (Payment Card Industry Data Security Standards). Organizations with current backups who were impacted by malicious ransomware have been able to recover and return to operations with minimal impacts.
Add advanced endpoint protection. Always-on tablets, laptops, and mobile devices make soft targets for attackers. It only takes a single user or misconfigured device for attackers to gain malicious access. Managed services such as EventTracker SIEM with Endpoint Detection and Response (EDR) fortify your security and reduce attack surface that can make your organization and sensitive data vulnerable.
Enable visibility with full logging and monitoring. Today’s threat landscape demands more than a “set it and forget it” approach. Continuous monitoring 24/7 by cybersecurity experts provides early detection of targeted attacks as well as insider threats.
Our Approach
We understand that your website is crucial, representing your brand, building community trust, facilitating citizen services, and generating online revenue. Hackers are actively targeting websites with advanced tools that require advanced security to remain protected. A proactive approach to website security ensures compliance with regulatory mandates such as HIPAA (Health Insurance Portability and Accountability Act) and Protected Health Information (PHI). SOC-as-a-Service (SOCaaS) provides 24/7 visibility from security experts with an award-winning Security Information and Event Management (SIEM) that strengthens your website defenses, controls costs, and optimizes your existing IT and Security teams.
Conclusion
Constant internet connectivity provides opportunity for innovation and modernization, but also presents an opportunity for potential cybersecurity threats that can compromise your most valuable asset: customer and financial information. Your website is vital for brand visibility and to conduct business. It is crucial to maintain site security and access to the rest of your organization’s data and valuable assets. While there is no silver bullet, we covered some practical countermeasures to help you Own IT. Secure IT. Protect IT. and reduce the likelihood of website attack. Learn more in this SOC Catch of the Day that demonstrates how Netsurion keeps organizations safe from advanced web threats.


