5 min read
The old Haunted Hotel with squeaky wood floors, welcomed all guests who dared enter the front doors. Guests arrived from every nation – every corner of world – ready to spend money and explore.
Once Vlad the Impaler’s castle, the building is a fortress, but they had since expanded to a vast empire of Haunted Hotels. Even after the age of online payments and technology, they operated with the assumption that nothing could penetrate their walls or systems. It all worked like a charmed-spell, day-in and day-out, from front-desk and online transactions to room service, restaurants, sundries, and the spa.
Sure, they had cyber goblins, witches, and the like. But that was all folklore…{gulp} right?
As legend goes, the hotel has a past…the grim reaper of retail – Breach the Blob – tarnished the Haunted Hotel’s foundation and reputation with gooey sludge that seemed to stick everywhere.
Breach slithered undetected for months and months, allowing its goo-filled malware mites and ransomware rats to infect every terminal, system, and device. That gross blob even spread to other Haunted Hotel locations across the world, easily.
The mess buried the hotel brand and owners for some time, and was quite the cleanup effort. Many files were lost, including the cost of a revenue hit, law suits, and most importantly, consumer trust. They thought they were PCI compliant (turns out not so much), so auditors continued the burial until the hotel was almost not able to recoup.
Emerging from the ground, determined to get through it, the hotel brand and franchise owners dusted off the dirt and got to work. They conducted due diligence to thwart a repeat of its breach-haunting past.
The hotel had done everything right (or so they thought) to keep the malware mites and point-of-sale (POS) ransomware rats away. They had a firewall in place and anti-virus capabilities installed.
Even in the Cloud, they felt secure, as long as their in-house Ghost Security Officer, Anti-Virus, was around. Day in and day out, Anti-Virus feverously inspected each and every system, comparing against the Most-Wanted list to protect against Breach and its brutes.
It had been so long since the last Breach sighting that they had gotten a little too comfortable. Plus, Haunted Hotels operated with the notion that they are bigger now with more protection, it won’t happen to them (when they were small they also thought it wouldn’t happen to them – they were too small to be a “target”). We all know being small actually made them a nice target.
During the time Breach first hit, they were lucky to get unburied from the mess and recoup. Most small businesses wouldn’t have made it past dawn with Breach the Blob trespassing.
The old Haunted Hotels were as successful as ever, and this haunting was behind them. Then the unthinkable happened again, but this time Breach brought friends.
It was a clear black night with the full moon casting a bright eerie hue. The guests were buzzing with chatter in the hotel bar and restaurants, while others were settled in for the night.
Anti-Virus, the resident Ghost Security Officer, was always visibly stressed, but tonight he looked like he’d seen another ghost. Anti-Virus had failed and he knew it, but was trying hard not to let on (hey – he’s got his wife and two little goblins at home to think about; he can’t lose his day job).
Although Anti-Virus and the firewall protect against the grim reaper in some ways, that creep Breach was several steps ahead. It slithered in, undetected by those humans running things.
Even though Anti-Virus knew, he certainty couldn’t tell anyone – he’s a ghost for creepsake, and he’s got goblins to feed. Breach knew this – and he knew the vulnerabilities. Plus, the best vulnerability of all – the human being.
As nightfall turned to day, that creep Breach had:
- Stolen 70,000+ customer credit card numbers and personal data
- Lured in a POS ransomware rat that held all of the Haunted Hotel’s POS systems hostage, rendering them useless, and costing $20,000,000 per day in lost revenue
- Invited a “man in the middle” (MITM) to creep into people’s rooms, invading their smartphone connection and spying on them via their webcam
- Muddied the back-office connected systems with malware – trojans, viruses, and worms
- Assaulted with a “drive-by download” from an employee’s computer
Now WAKE UP. Yes, it was a terrible dream. A nightmare in fact. Luckily for Haunted Hotels, they had more up their sleeve.
Little did Anit-Virus know, they were being watched all along by the Chief Ghost Security Officer, SIEM (known as ‘security information event management’ by close friends and relatives). SIEM has capabilities that are like kryptonite to a creep like Breach. It can not only find and track an attack in real-time, SIEM protects every endpoint of every system in place, from location to location. And alerts those humans to threats so they can do something about Breach before he infects anything else.
The moral of the story?
Anti-virus, firewalls, and P2PE are not enough when dealing with ‘breaches’ like Breach the Blob. The Haunted Hotel story only spins yarns about some of the threats out there… watch your back – there are many, many more.
Even vendors you use, that get breached, can impact you and your business due to the system connections. And insider jobs? Humans aren’t perfect and cybercriminals know it. They prey on the weaknesses within our system defenses and on the imperfections of human beings. Due to this, it’s not possible to stop all attacks, but you can be ready to defend against them.
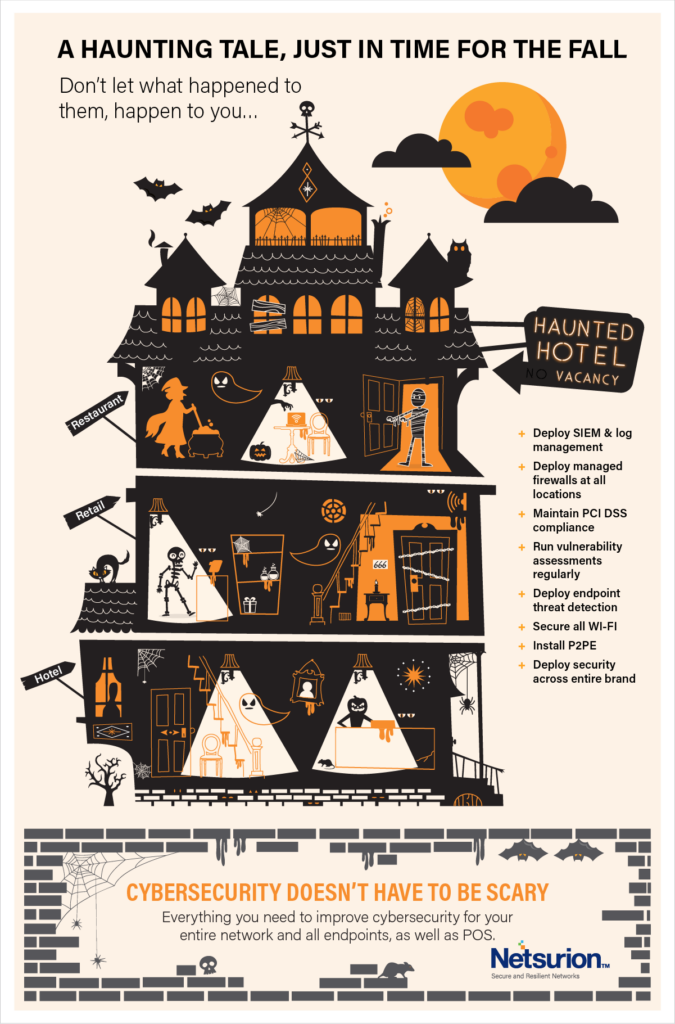
Security within your business is your responsibility. So is your customers’ data. The moral of the story? Deploy Netsurion’s comprehensive suite of cybersecurity solutions, then you can say: “What’s up breaches? We’re ready for you.”
In a world of fear… cybersecurity doesn’t have to be scary
Get informed and stay informed with our monthly webcasts about educational cybersecurity topics. Fill out this form to get a Free Security Assessment and to be added to our newsletter and webcast invitations.


