2 min read
Analyzing all the login and pre-authentication failures within your organization can be tedious. There are thousands of login failures generated for several reasons. Here we will discuss the different event IDs and error codes and how you can simplify the login failure review process.
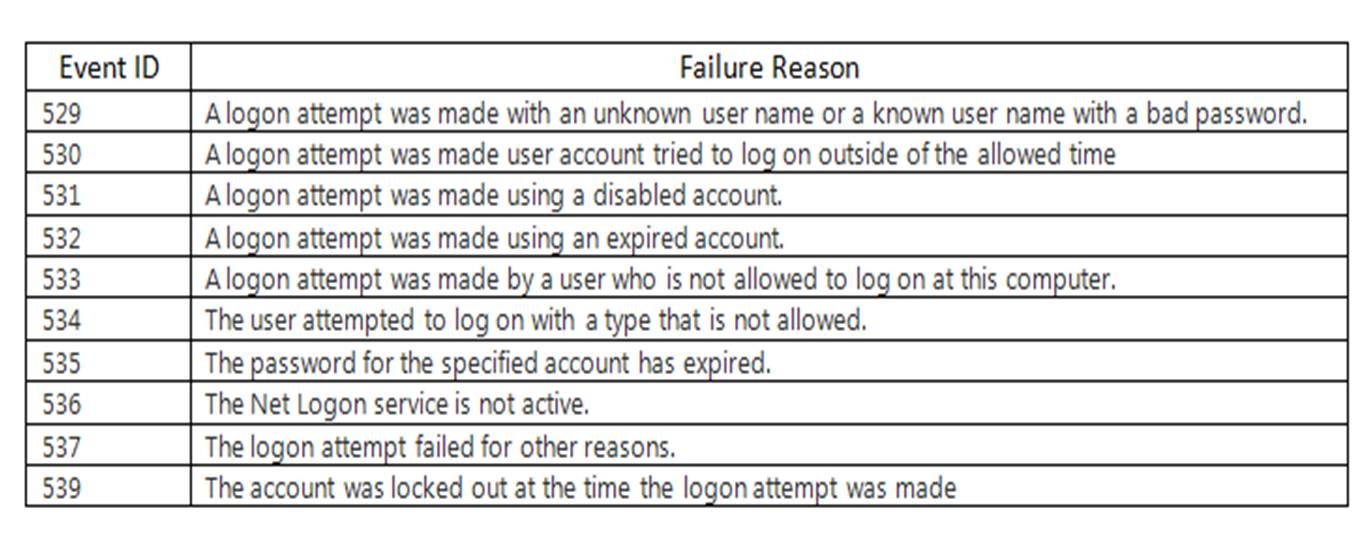
First you need to know the event IDs related to login and pre-authentication failures.
The login failure event IDs are: 529, 530, 531, 532, 533, 534, 535, 536, 537 and 539.
A sample event description for event 529 is:
Logon Failure
Reason: Unknown user name or bad password
User Name: %1
Domain: %2
Logon Type: %3
Logon Process: %4
Authentication Package: %5
Workstation Name: %6The Windows 2003 server adds some extra fields in the event description:
Caller User Name:-
Caller Domain:-
Caller Logon ID:-
Caller Process ID:-
Transited Services:-
Source Network Address:10.42.42.180
Source Port:0NOTE: The only difference in event IDs 529, 530, 531, 532, 533, 534, 535, 536, 537 and 539 is the reason for failure. See below:
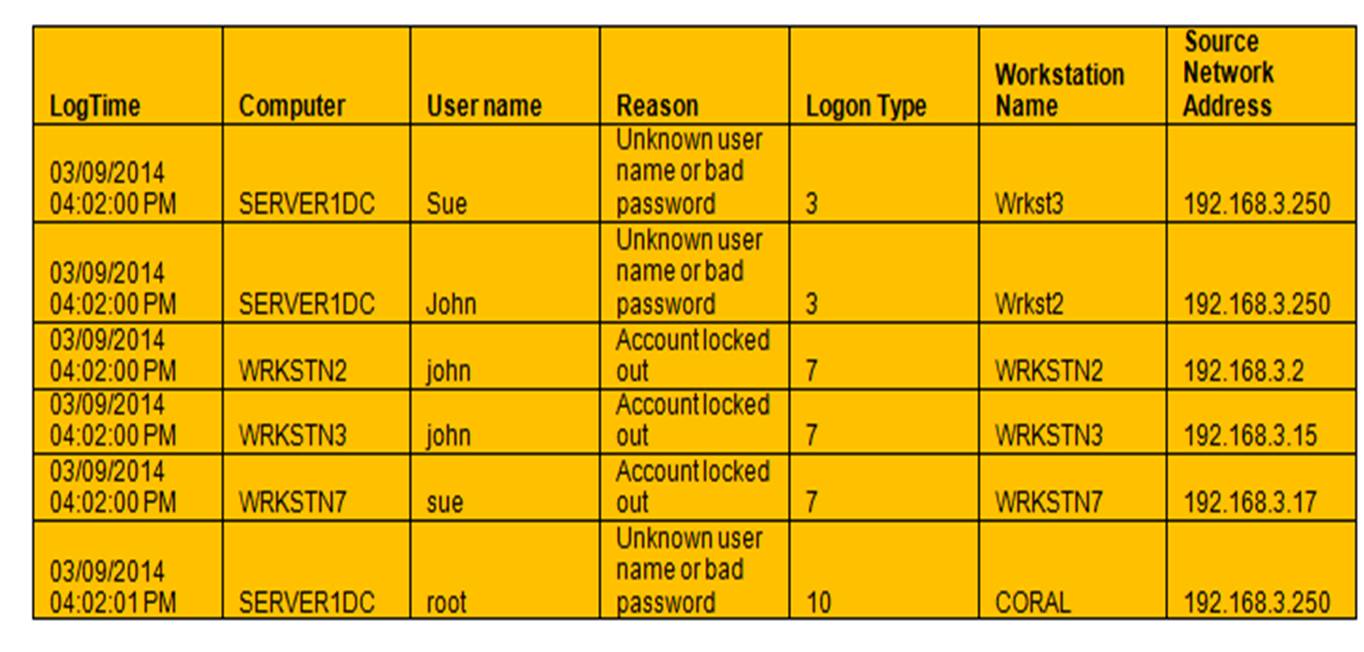
So how do we analyze these events efficiently and effectively? You need to look within the event description. In the login failure event description we only care about the failure reason, user name, logon type, workstation name and source network address. The rest is all noise.
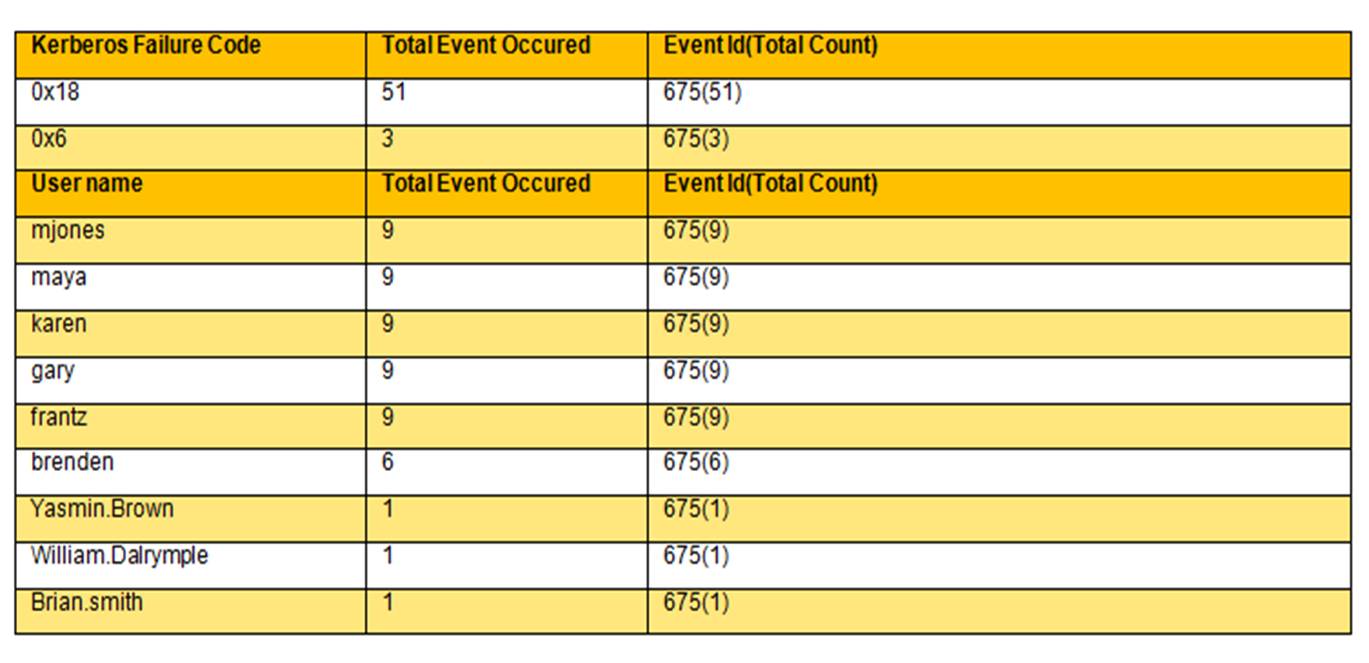
If you create a flex report with EventTracker, it will only display the required fields instead of the whole report. It also provides a summary based on the total number of events for each failure type and user name. See the sample below:
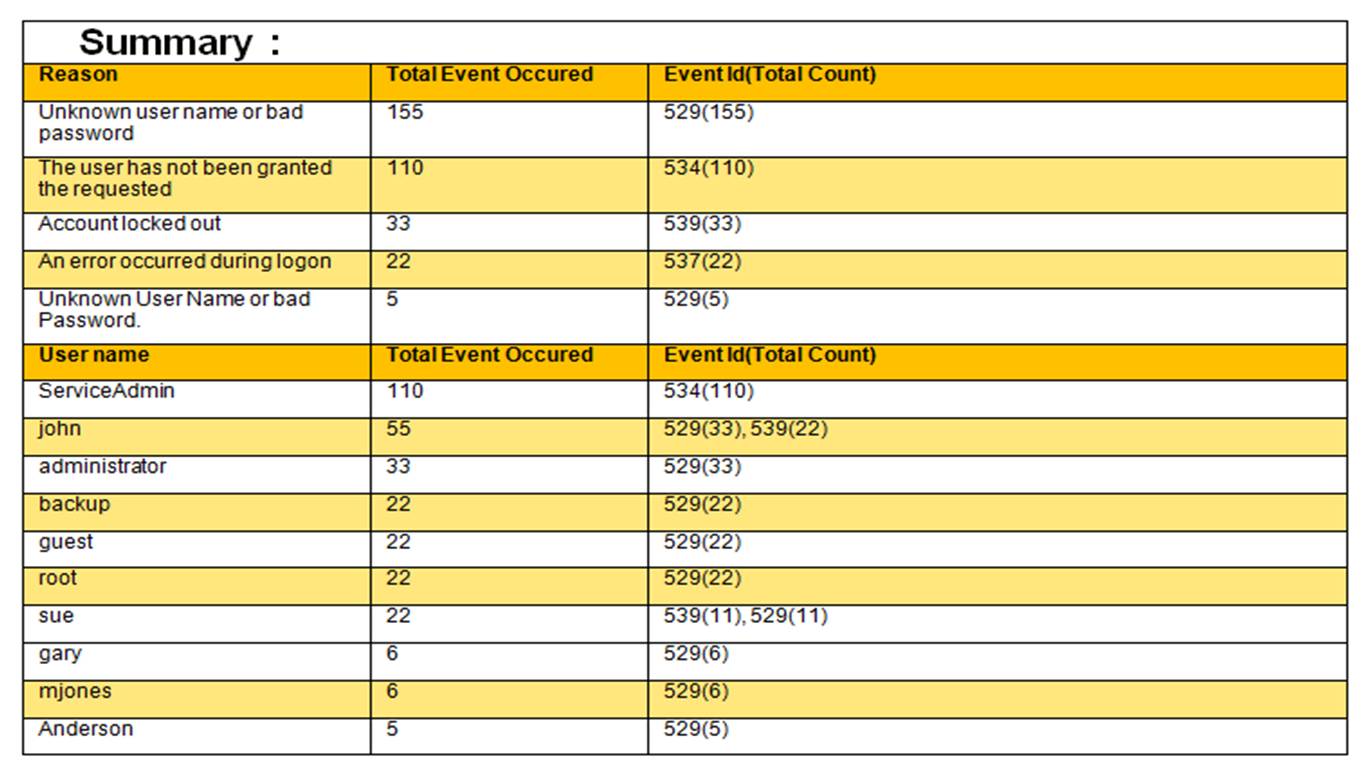
Instead of going through hundreds of pages of a lengthy report, the report below provides a quick analysis on login failures based on failure reasons and user name. This allows you to efficiently and effectively analyze login failures in your environment.
Details
Now let’s discuss the pre-authentication failure event.
Pre-authentication failure event id is: 675.
User Name: %1
User ID: %2
Service Name: %3
Pre-Authentication Type: %4
Failure Code: %5
Client Address: %6Here it is very important to analyze failure codes. There are tons of failure codes. I would recommend concentrating on the below:
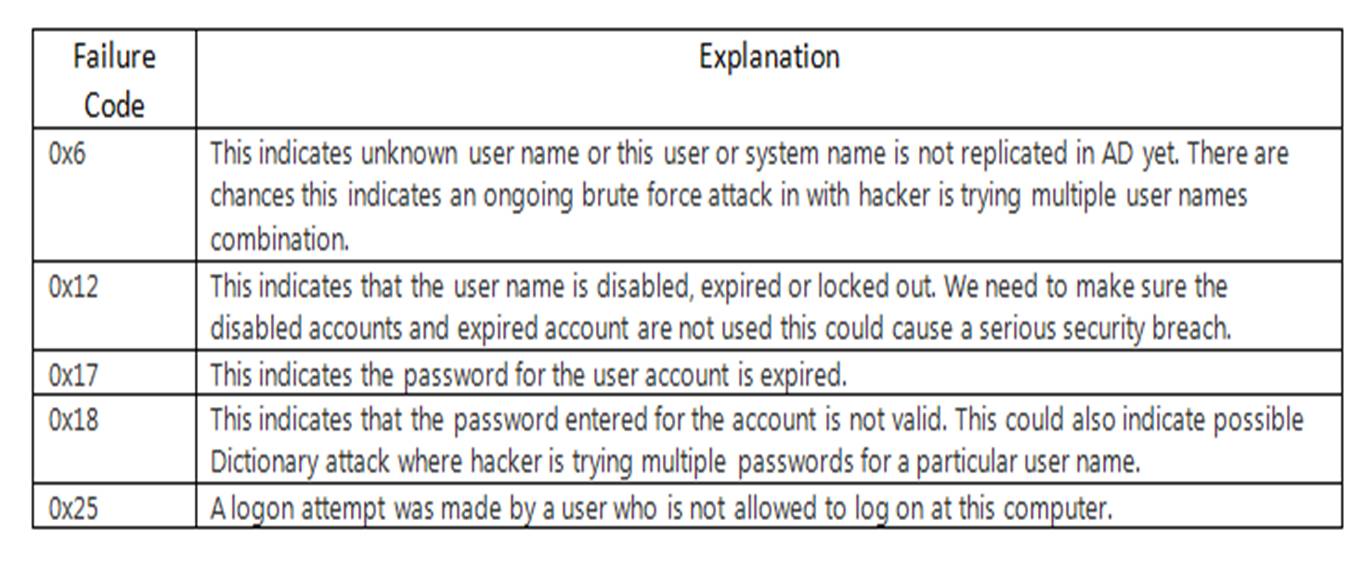
I would recommend using the same flex report format that we did above to get the summary counts based on failure code and user name.
Details
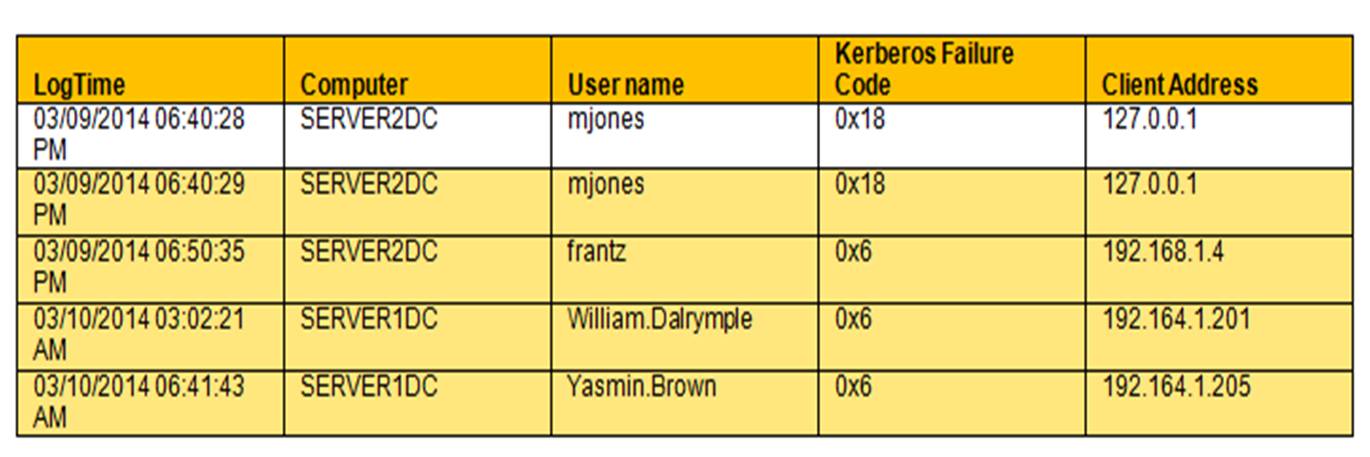
This demonstrates that it is very efficient and effective to analyze pre-authentication failures using this method versus the traditional way, which doesn’t allow you to know how many failures were associated with each username or how many respective failure codes (summary counts, etc.) there were, nor how many failures were associated with one particular workstation, etc. Analyzing the traditional report for hundreds of events every day becomes nearly impossible.


