3 min read
Advances in data analytics and increased connectivity have merged to create a powerful platform for change. Today, people, objects, and connections are producing data at unprecedented rates.?According to DOMO, 90% of all data today was created in the last two years with a whopping 2.5 quintillion bytes of data being produced per day. With more Internet of Things (IoT) devices being produced, new social media outlets created, and the increasing number of people turning to search engines for information, the numbers will continue to grow.
So, what do we do with this overwhelming amount of data? Big data may be analyzed to reveal patterns, associations, and trends. Big data is the engine of data analytics growth and in most big data circles is defined by the Four Vs below.
- Volume: massive and passively generated
- Variety: originating from both individuals and machines at multiple points in the data value chain
- Velocity: generally operating in real time
- Veracity: referring to the uncertainty due to bias, noise or abnormality in data
Smart Questions
In a reasonably sized network, log data can be big data, but how do you extract value or intelligence from it? That has more to do with analytic capability and the ability to ask smart questions.
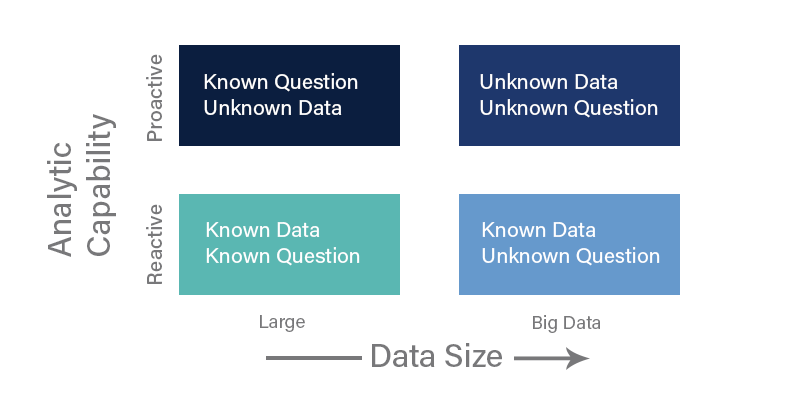
Known Data Known Question, the lower left quadrant, is for optimizing data standardized processes and procedures. The data sources are known, leaving the only question of timeliness and data quality.
The Known Data Unknown Question, the lower right quadrant, is best suited for domain experts such as our EventTracker Enterprise SOC team to discover questions they didn’t know to ask. It’s part of the “threat hunting” model. You go into the known jungle but cannot say what you will find. Once you stumble upon an anomaly, you move up/down and sideways to outline the contours and study the adjacent data till the entire kill-chain is revealed.
The Known Question Unknown Data, the upper left quadrant, is about pre-defined queries and reports that have been learned from past experiences or at other installations. They produce questions that are worth asking and in search of data to be asked against. A value-add of a co-managed SIEM is community intelligence. Once the community is aware of a certain pattern of attacks at one installation and uncover it, the lessons are rapidly applied to others to determine if similar attacks have or are occurring there.
The Unknown Data Unknown Question, the upper right quadrant, is the domain of machine learning or explorative or predictive computing. EventTracker uses the same Elasticsearch engine as a data store. Work is underway to leverage this investment to automatically model the behavior of your data – in real time to identify issues faster, streamline root cause analysis, and reduce false positives.
As the saying goes, it’s not what you have but what you do with it, that counts. Our EventTracker Enterprise Co-managed security service extracts actionable intelligence from big data for more effective security monitoring, threat detection, and incident response. Unlike other solution, you don’t just get technology, but outcome!


