10 min read
There are three cybersecurity “givens” that small-to-medium-sized businesses (SMBs) often face. One is you are not too small to be targeted by cyber criminals. Even big ransomware gangs are refocusing their efforts on mid-sized victims to avoid scrutiny. A second is that your attack surface is expanding – particularly with the move to cloud, Software-as-a-Service (SaaS) adoption, and Work-From-Home (WFH) – while threat actors continue to evolve new, more sophisticated approaches. The third is that you probably have too many cybersecurity tools and vendors to be effective. One Ponemon study found that companies deploy on average 47 different cybersecurity solutions and technologies. That’s in large part because new security measures tend to get deployed one by one. They’re either newly available technologies or point solutions to emerging cybersecurity threats and vulnerabilities. The resulting sprawl in security operations can actually decrease cybersecurity effectiveness when you don’t have the expertise and resources to manage all the tools, or the people and time to interpret and act on the analytics they generate.
The Cure for Sprawl is Consolidation
The cure for this technology and vendor sprawl is consolidating cybersecurity tools and vendors to simplify your security operations. For example, look for instances where there are overlapping capabilities between vendors. To consolidate, choose a partner that has both the breadth of cybersecurity technology and depth of cybersecurity expertise to handle multiple functions.
Lack of resources to monitor and evaluate the flow of data from your security infrastructure is a common problem for SMBs. Consider consolidating log data and forwarding it to a SOC-as-a-Service provider. These security vendors can apply expertise plus advanced tools such as AI to monitor log data 24×7 and alert you to events that require your scrutiny. This frees up your staff to focus on the matters that are critical to protecting your assets as well as providing around-the-clock coverage.
Defense-in-Depth: A Method for Uncovering Consolidation Opportunities
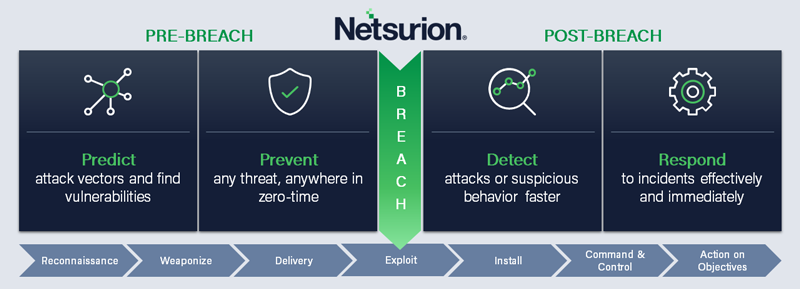
Before you can make fully informed decisions about consolidation, you need to consider your entire cybersecurity infrastructure and vendor network. One approach is to organize your analysis around the defense-in-depth threat cycle, which provides an end-to-end approach to managing security before and after the “boom” (a security incident). With this approach, you can identify overlaps as well as gaps in a multi-layered approach to cybersecurity.
Left of Boom: Predict and Prevent
While you can’t eliminate risk entirely, you can reduce it or proactively manage it pre-breach by minimizing the likelihood of a cyber attack.
Predict: The predict phase of defense-in-depth focuses on understanding your attack surface and efficiently managing vulnerabilities. Does your vulnerability management solution include remediation recommendations as well as scanning and reporting, so you can take action when vulnerabilities are discovered? How are you incorporating new devices and resources such as cloud and containers? Can your vulnerability management provider also deliver actionable threat intelligence based on threat data feeds from partners and open-source providers?
Vulnerability management and patching are foundational to any security program’s left-of-boom capabilities. The value lies in getting actional mitigation steps from scanning that you can execute effectively and efficiently. However, vulnerability management is often neglected internally because limited resources are focused higher up the tech stack, and it’s painful to disrupt the business to do the necessary scanning. A trusted provider can take this off your hands and ensure that scanning takes place consistently and at your convenience to minimize interruptions.
Prevent: How deep and broad is your endpoint protection? Do you have multiple vendors in this space to cover all physical endpoints (including all widely used endpoint operating systems and file types) as well as virtual desktop solutions like Amazon Workspaces and virtual desktops from Citrix, VMware, and Microsoft? If so, can one vendor cover all endpoints with a single solution?
And does that one vendor also provide threat hunting within your environment to protect you against the most evasive known and unknown threats? Many of these threats, including ransomware and advanced persistent threats, sit in a victim’s environment for days or weeks before a payload is activated. Threat hunting, particularly solutions that employ both human and artificial intelligence, can help prevent the boom.
Right of Boom: Detect and Respond
Take steps post-breach to reduce the impact of a successful cyber attack.
Detect: XDR, which stands for Extended Detection and Response, has experienced growing adoption. XDR is all about consolidation. It combines multiple capabilities such as NDR (network) and EDR (endpoint) under the “X” moniker. So, if you currently have multiple vendors for a myriad of detect and respond solutions, you are in a great position to simplify your security operations by going with a single vendor that can truly deliver consolidated visibility and management.
For the detect component of XDR, you want to make sure a provider’s solution includes a SIEM (Security Information and Event Management) component to aggregate log data from across your environment (network, endpoints, cloud) for real-time analysis. Managed solutions should include SOC-as-a-Service, to provide expert review of rule-based alerts from the SIEM.
An Intrusion Detection System (IDS) also plays a critical detect role in those first minutes after the boom by identifying unusual patterns or anomalies in your network and systems. To be effective, an IDS needs continuous tuning to keep up with the emerging threat intelligence. The provider’s Security Operations Center (SOC) offers actionable insights about malicious activity. SOC specialists in behavioral analysis analyze anomalies in human activity detected within the network, such as accessing sensitive data or initiating downloads, to help guard against insider threats.
Respond: Respond is the “R” in XDR. Part of your response capability should be automated to provide real-time blocking of suspicious activity before any damage is done. Response automation like Application Control is one example of how to terminate suspicious activity. Ideally, the service provider you choose for consolidation will include Incident Response support as well, including customizing playbooks to your environment. Look for a provider that collaborates with you and provides timely support while you maintain hands-on-the-keyboard mitigation responsibility. And if you have other strategic priorities to manage or lack the staff or skills, look for a Managed Security Service Provider (MSSP) with a 24×7 Security Operations Center (SOC) that can augment your team.
The Final Note: Platform Versus Conglomeration
When you are considering consolidating vendors, look at how your candidates came to offer more than a single-point solution. It is not unusual in the security marketplace for companies to grow by acquisition, in many cases offering a conglomeration of disjointed point products or services under the guise of a consolidated solution.
Netsurion takes a managed platform approach, the benefit of which is that capabilities are unified at the core and accessed from one centrally managed console. Our defense-in-depth capabilities work together to predict, prevent, detect, and respond to threats across your business. Learn more about defense-in-depth with Netsurion Managed Open XDR.


