2 min read
The cybersecurity threat landscape is in constant motion – ever evolving. According to Kaspersky Labs, 323,000 new malware strains are discovered daily! Clearly, this rate of increased risk to a company’s assets and business continuity warrants a smart investment in cybersecurity. Unfortunately, many companies are not keeping pace with their increasing risk, nor could they ever be expected to if their leadership views cybersecurity as a cost center while still viewing other innovations, such as digital transformation, as an investment.
For any digital transformation project to be successful and return the anticipated value, cybersecurity must be considered foundational.
Just as that new $500 suit is an investment to help you get that new job, the cost to have it tailored is part of that investment. The same goes for digital transformation and cybersecurity. But for many companies, the digital transformation is long underway, and cybersecurity desperately needs to catch up. That new suit needs to be tailored quickly before another person sees you in that poor-fitting getup.
A successful cybersecurity strategy is without much hope if executive leadership does not champion the proper investment and prioritize the efforts. The result is too often organizations piecemealing pointed IT security solutions one-at-a-time, failing to prioritize wholistic cybersecurity projects. This only exacerbates the risks to the business, but also hampers the efficiency in accomplishing other technology projects deemed as competitive differentiators.
So, where do you start to improve your cybersecurity posture ASAP?
- Get executive support immediately so you don’t spin your wheels on half-baked inefficient IT security practices.
- Change the mindset by showing cybersecurity is an investment in the company’s future.
- Keep in mind the cybersecurity triad of “platform, people and process”, and seek complete solutions that can ensure long-term success.
Here are some tools to help you along your journey…
Cybersecurity Maturity Model
It’s important to take a step back and understand where you are today, where you should be, and where you want to go next. By considering all four key aspects of a complete security architecture – prevent, detect, respond, and predict – a good Cybersecurity Maturity Model provides a practical stair-step approach toward the appropriate level for your organization.
![img cybersecurity maturity model ops[1]](https://www.netsurion.com/assets/content/uploads/img-cybersecurity-maturity-model-ops1-1-1024x451.jpg)
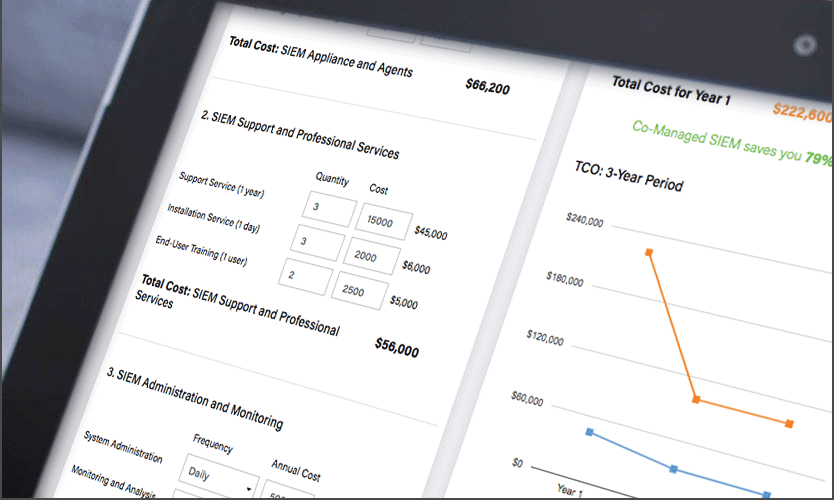
SIEM Total Cost of Ownership Calculator
Security Information and Event Management (SIEM) is the foundation of any well-grounded IT security strategy. However, depending on your organization’s unique requirements, staffing, and deployment situation, the total cost of SIEM can vary widely. Use our SIEM TCO calculator to compare 1-year and 3-year costs of self-managed and Co-Managed SIEM solutions.