4 min read
Microsoft 365 is immensely popular across all industry verticals in the small-to-medium-sized business (SMB) space. It is often the killer app for a business and contains valuable, critical information about the business. Accordingly, Microsoft 365 resiliency and defense are top concerns on IT leader’s minds.
Is Microsoft 365 defense totally up to the vendor, Microsoft, and the user has no responsibility? Hardly. Microsoft is merely providing the software-as-a-service, hosted on their infrastructure. While they do have some responsibility for securing the infrastructure and keeping the application up to date, you are the admin and it’s your data; therefore it is your responsibility to secure your tenant.
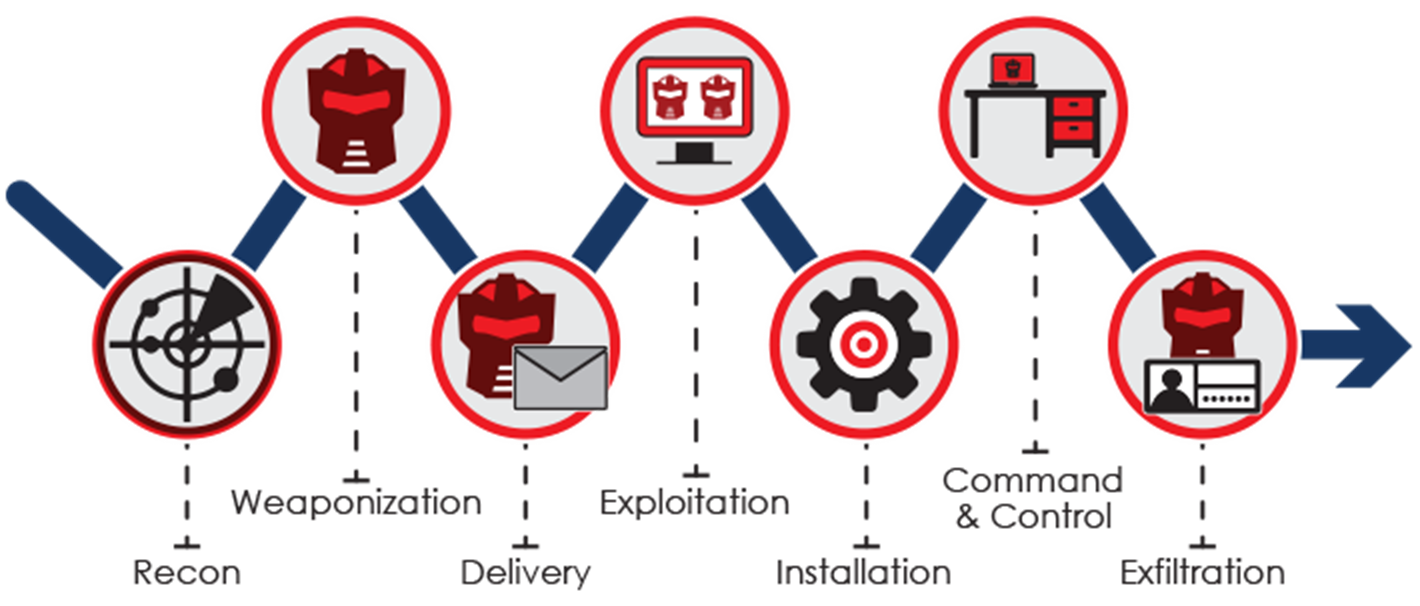
While the motivations and capabilities of attackers vary widely, most attacks still follow a common process, a basic pattern, and proceed from one step to the next to achieve the desired outcomes. This step-wise process can be defended against by focusing defense measures on choke points in the chain. Of course, any step can be bypassed through exploit technologies, so the best strategies apply defenses at every step along the threat chain that is shown below.
Concern 1: Data Exfiltration
Microsoft 365 encompasses many different types of data including: Email, documents, Teams converations and SharePoint data. In fact, even breaching your Active Directory information can be useful to an attacker. Data can be stolen in any number of ways, including through a breach of an account with access to the data, or through system and infrastructure attacks that give them local or system admin privileges to computers that store the data outside of Microsoft 365. Why would cyber criminals want to do this? Many reasons such as the theft of intellectual property, the desire to blackmail you, the intention to sell your data on the black market, or to use the data to further entrench themselves in your systems.
Prevention: Focus on not just the data, but also the accounts needed to access the data. Enforce least privilege, establish access control lists, define external sharing policies, and use data classification schemes to identify high risk data.
Detection: Finding a breach is complicated because it is difficult to distinguish normal usage from abnormal usage patterns, especially since the data will most likely be accessed with an account that has the needed privileges. Out-of-ordinary behavior detection within Security Information and Event Management (SIEM), platforms are useful in such cases. Especially when reviewed by experienced eyes to catch anomalous interactions with data, especially for large downloads. Conversely, attackers can also use a “low and slow” approach to avoid detection and remove data slowly, especially if they are knowledgeable insiders.
Remediation: This is the hardest attack scenario to fix because the cat is already out of the bag. Two things to focus on
- Identify how the exfiltration happened so that you can stop it
- Have an incident response (IR) plan for how to deal with the impacts of losing control of the data and practice it annually
Concern 2: Privilege escalation and lateral movement
The attacker has managed to compromise one or more accounts in your tenancy and is now working towards global administrator privileges.
Prevention: Make your global administrator community small; a minimum of two and a maximum of five for any size of tenant. Require multi-factor authentication (MFA) for global administrators, and regularly review activity of such users.
Detection: The key here is to monitor activity. This type of attack causes anomalous activity that deviates from a well-understood baseline.
Remediation: Enable multi-factor authentication. Examine everything that the attacker has done to your data and what they have done to further entrench themselves in your tenancy. Look for new accounts that have had recent changes (such as promotion to tenant admin), global configuration changes, and every interaction with data from the affected accounts.
Concern 3: Account compromise
An account in your Microsoft 365 tenant is breached such that it can be used by an attacker to interact with either resources in Microsoft 365, or with your on-premises infrastructure. There are a variety of ways that this can happen including spear phishing for credentials with harvesting websites, or spear phishing with malware to install rootkits and keyloggers.
Prevention: Use high quality authentication mechanisms such as passwords and MFA. Monitor for multiple failed logon attempts.
Detection: The key to an effective account breach detection is understanding what a normal pattern of activity looks like for your users. There are several features that exist in the activity data that you can use to find illicit or anomalous activity. For example, the data includes the following: IP addresses (which can be correlated to geographies), date and time, the specific action performed, and user agent.
Remediation: Enabling Multi-Factor Authentication (MFA) is a common, and powerful, remediation to keep the account safe after it has been breached. Monitor the account for a period of time to ensure it hasn’t been re-breached.
While Microsoft has provided guidelines on how a user should secure their Microsoft 365 tenant, making sure everything is secure and remains secure can become complicated and is time consuming. Looking for IT and cybersecurity simplicity? We make securing Microsoft 365 and your systems easier by providing predefined reports, dashboards, and alerts via the Netsurion Managed Threat Protection solution. The service is backed by a 24/7 Security Operations Center (SOC) to be ever vigilant.


