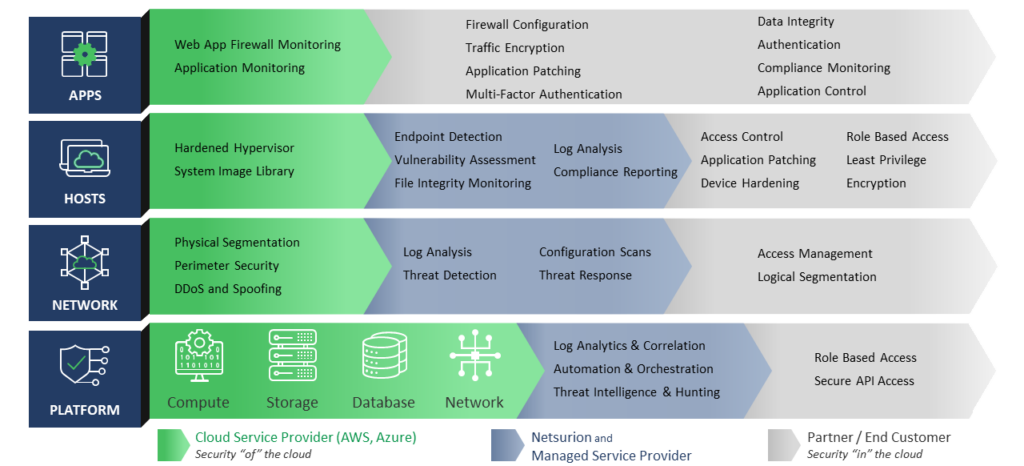
Shared Cloud Security Model
Your organization’s cloud environments are mission critical. User productivity and effectiveness depend on Amazon AWS, Microsoft Azure, and more. In cooperation with public cloud vendors, we restore visibility to user, application, and data behavior through audit/logging, PowerShell activity tracking, and a 24/7 SOC to detect and escalate incidents. Netsurion alerts you to cloud security problems and recommends mitigation steps long before a disastrous failure occurs.
Centralize Cloud Visibility and Security
Your move to the cloud expands your attack surface and necessitates a move to more advanced security. Microsoft security is just a starting point. Netsurion makes security easier by providing 24/7 monitoring, rapid alerts, comprehensive reporting, and executive dashboards.
Benefits include:
- Enhanced security coverage no matter where your data resides
- Unified view of risk with single-pane-of-glass visibility
- Faster detection of threats and malicious activity
- Expanded coverage that scales as your infrastructure grows
- Additional cost savings with a centralized approach to cybersecurity

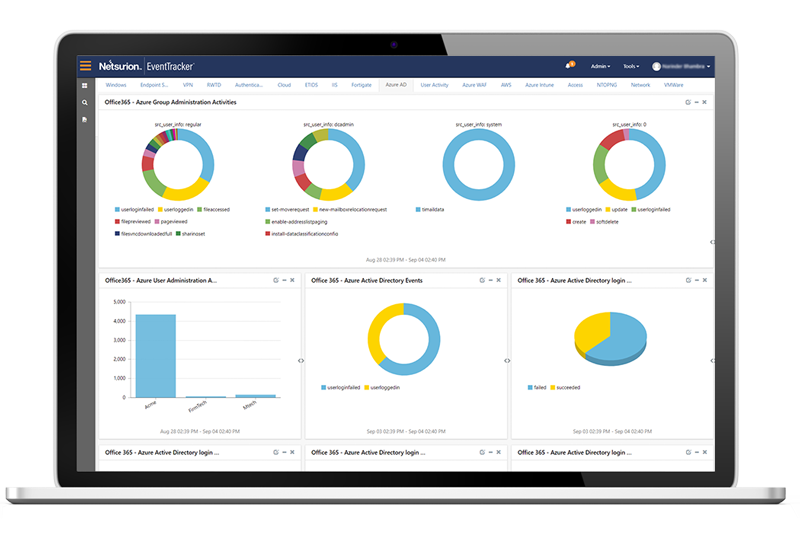
Safeguard Azure Active Directory
Microsoft Azure Cloud Platform provides a range of cloud services, including compute, analytics, storage, and networking. At any point in time, Azure Cloud, like all cloud platforms, is under attack by cyber criminals aiming to compromise key systems. Netsurion can help to avoid and learn from these cyber-attacks.
- Monitor: the actions performed by users and detect unusual changes to passwords and policies, user administration activities, PowerShell activity tracking, events from the Azure App Services, sign-ins from multiple geographies or unknown sources, all with centralized reporting in the Netsurion console
- Track: user login activities to Microsoft with geo-location for identifying compromised accounts
- Identify: suspicious login attempts and receive an alert when a first-time user login occurs from a new location or suspicious IP address, delete and update actions for the Azure Kubernetes instances, user actions in Azure Storage, geo-location to modify and delete actions performed, and identify access to storage with the status codes
- Detect: brute force login attempts using geographic information such as countries where your organization does not operate
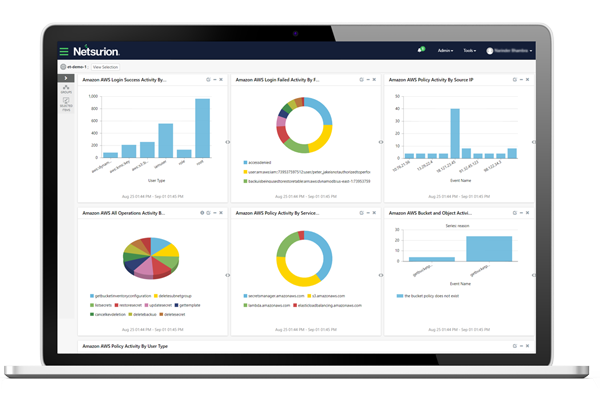
Safeguard Amazon Web Services (AWS)
Amazon Web Services (AWS) provides on-demand cloud computing platforms and APIs to individuals, companies, and governments. To fend off attacks, Netsurion will:
- Monitor: PowerShell activity tracking, user actions and administrative activities, sign-ins from multiple geographies or unknown sources, all with centralized reporting in the Netsurion console
- Track: user login activities to Amazon/AWS with geo-location for identifying compromised accounts
- Identify: suspicious login attempts and receive an alert when a first-time user login occurs from a new location or suspicious IP address
- Detect: brute force login attempts using geographic information such as countries where your organization does not operate
Shield Cloud Environments from Hackers
Organizations now rely on the cloud for primary means of communicating with employees, suppliers, and customers. Netsurion helps safeguard the flow of email to keep your “always on” organization up and running.
- Audit administrator actors, including mailbox creation and mailbox deletion
- Monitor changes to Microsoft 365 Exchange policies that might result in a security gap such as malware, spam, and spoofed emails
- Identify users accessing mailbox folders, purging deleted items, and accessing other mailbox accounts
- Trace emails to track the organization’s mail flow
- Monitor PowerShell activity tracking
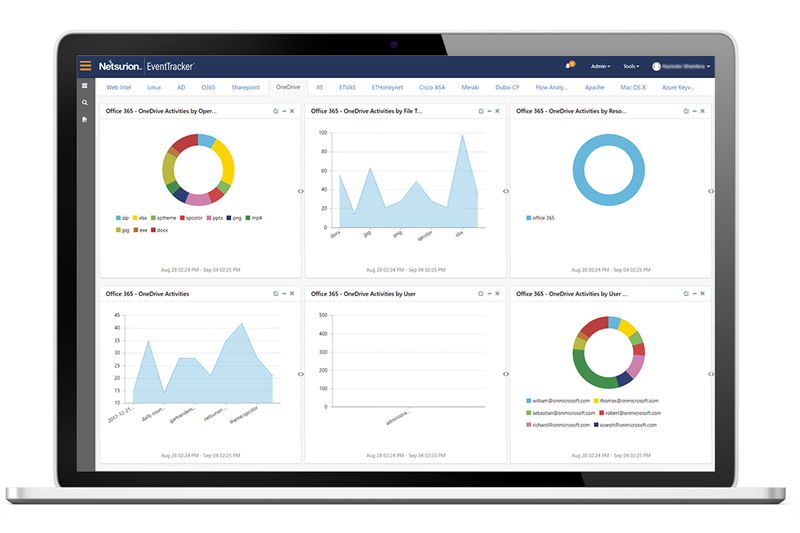
Protect Sensitive Data Stored in the Cloud
A 24/7 SOC to watch for and escalate alerts is crucial to detect suspicious activities that may signal information leakage or a costly data breach:
- Monitor public cloud environments and review suspicious administrator actions such as site added, deleted or modified
- Monitor activities such as files shared with external users as well as file upload and download status
- Generate comprehensive reports for hands-on users and executives
Success Stories
Our security operations center and AI-driven threat protection platform review billions of logs daily to defend customers from advanced threats. Here are just a few real-world examples.