Active Exploitation of SolarWinds Software
Published: December 17, 2020, 10:00 am EST
US-CERT.CISA
Cybersecurity and Infrastructure Security Agency (CISA) has issued an alert on Active exploitation of SolarWinds Orion Platform software versions 2019.4 HF 5 through 2020.2.1 HF 1, released between March 2020 and June 2020.
Description
This attack was likely conducted by an outside nation-state and intended to be a narrow, extremely targeted, and manually executed attack, as opposed to a broad, system-wide attack. We recommend taking the following steps related to your use of the SolarWinds Orion Platform.
Determined Impact
An attacker who successfully installs trojanized SUNBURST backdoor components could perform file transfers, file execution, disabling system services, and gathering system information.
Why it is Critical?
The attacker’s post compromise activity leverages multiple techniques to evade detection and obscure their activity, but these efforts also offer some opportunities for detection.
Affected Components
SolarWinds Orion Platform software builds for versions 2019.4 HF 5 through 2020.2.1 HF 1
Mitigations/ Workarounds
Security Updates
SolarWinds recommends upgrading to Orion Platform version 2020.2.1 HF 2 as soon as possible to ensure the security of your environment. The latest version is available in the SolarWinds Customer Portal.
Workarounds
If you cannot upgrade immediately, please follow the guidelines available here for securing your Orion Platform instance.
The primary mitigation steps include having your Orion Platform installed behind firewalls, disabling internet access for the Orion Platform, and limiting the ports and connections to only what is necessary.
Required Actions
- SolarWind recommends taking the following steps related to your use of the SolarWinds Orion Platform: Solarwinds-security advisory
- Update any of the products listed as known affected for Orion Platform v2020.2 with no hotfix or 2020.2 HF 1 to upgrade to Orion Platform version 2020.2.1 HF 2 as soon as possible to ensure the security of your environment. This version is currently available here.
- SolarWinds asks customers with any of the below products listed as known affected for Orion Platform v2019.4 HF 5 to update to 2019.4 HF 6, which is available for download here.
- The hotfix release 2020.2.1 HF 2 is now available in the SolarWinds Customer Portal at customerportal.solarwinds.com. SolarWind recommend all customers update to release 2020.2.1 HF 2, as the 2020.2.1 HF 2 release both replaces the compromised component and provides several additional security enhancements.
- Kindly ensure that the best practices are followed to secure other version of Orion Platform deployments [Orion platform-Core-secure-configuration]
Monitoring Mechanisms
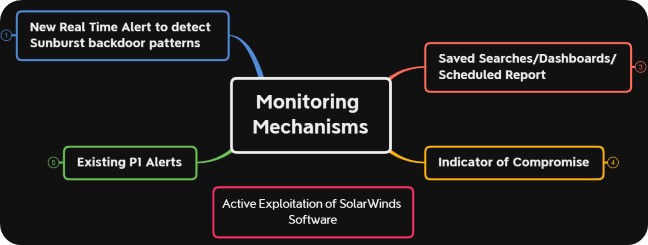
Alert Monitoring
- New real time alert [Netsurion: Sunburst backdoor component with SolarWind supply chain pattern] has been created to monitor Sunburst backdoor trojan component patterns.

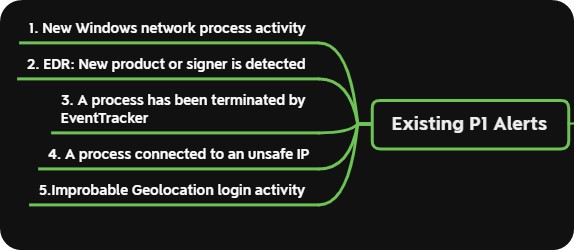
Existing P1 Alerts
- Netsurion: New Windows network process activity will be triggered when a new connection is observed to command and control server from installed trojan process based on the behavior.
- Netsurion EDR: New product or signer is detected will be triggered when a new product or signer is detected during the first time launch of SUNBURST components.
- Netsurion: A process has been terminated by Netsurion will be triggered when an identified bad Hash component launch is stopped by Netsurion agent based on the unsafe list.
- Netsurion: A process connected to an unsafe IP will be triggered when a connection is observed to unsafe IP addresses which are known to be involved in Command and control server.
- Netsurion: Improbable Geolocation login activity will be triggered when an unusual login is observed from few syslog sources.
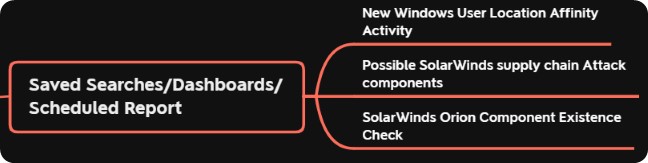
Saved Searches, Dashboards/ Scheduled Report
- Saved searches/Dashboards has been created to identify the SolarWinds component Existence and Sunburst backdoor trojan Attack pattern.
- Netsurion: New Windows User Location Affinity Activity will be helpful in monitoring remote login activities
Indicator of Compromise
- Netsurion Threat Center has been updated with Identified Bad MD5 Hash Values and IP addresses in order to detect the IP address communication and terminate process launches based on the unsafe list.
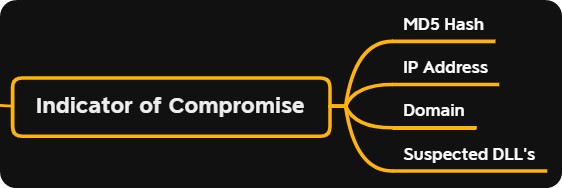
| IOC Type | Value |
|---|---|
| MD5 | 02af7cec58b9a5da1c542b5a32151ba1 |
| 08e35543d6110ed11fdf558bb093d401 | |
| 2c4a910a1299cdae2a4e55988a2f102e | |
| 846e27a652a5e1bfbd0ddd38a16dc865 | |
| b91ce2fa41029f6955bff20079468448 | |
| 4f2eb62fa529c0283b28d05ddd311fae | |
| 56ceb6d0011d87b6e4d7023d7ef85676 | |
| 3e329a4c9030b26ba152fb602a1d5893 | |
| e18a6a21eb44e77ca8d739a72209c370 | |
| IP Address | 54.193.127.66 |
| 54.215.192.52 | |
| 34.203.203.23 | |
| 139.99.115.204 | |
| 5.252.177.25 | |
| 5.252.177.21 | |
| 204.188.205.176 | |
| 51.89.125.18 | |
| Domain (Monitored with Saved Search/Dashboard) | deftsecurity.com |
| freescanonline.com | |
| thedoccloud.com | |
| websitetheme.com | |
| highdatabase.com | |
| incomeupdate.com | |
| databasegalore.com | |
| panhardware.com | |
| zupertech.com | |
| avsvmcloud.com | |
| digitalcollege.org | |
| virtualdataserver.com | |
| Exploited Components (Monitored with Real Time Alert) | solarWinds.Orion.Core.BusinessLayer.dll |
| app_web_logoimagehandler.ashx.b6031896.dll | |
| CORE-2019.4.5220.20574-SolarWinds-Core-v2019.4.5220-Hotfix5.msp |
| Known affected products |
|---|
| Application Centric Monitor (ACM) |
| Database Performance Analyzer Integration Module (DPAIM) |
| Enterprise Operations Console (EOC) |
| High Availability (HA) |
| IP Address Manager (IPAM) |
| Log Analyzer (LA) |
| Network Automation Manager (NAM) |
| Network Configuration Manager (NCM) |
| Network Operations Manager (NOM) |
| Network Performance Monitor (NPM) |
| NetFlow Traffic Analyzer (NTA) |
| Server & Application Monitor (SAM) |
| Server Configuration Monitor (SCM) |
| Storage Resource Monitor (SRM) |
| User Device Tracker (UDT) |
| Virtualization Manager (VMAN) |
| VoIP & Network Quality Manager (VNQM) |
| Web Performance Monitor (WPM) |
Reference Details:
- https://www.solarwinds.com/securityadvisory
- https://www.cisa.gov/news/2020/12/13/cisa-issues-emergency-directive-mitigate-compromise-solarwinds-orion-network
- https://www.fireeye.com/blog/products-and-services/2020/12/global-intrusion-campaign-leverages-software-supply-chain-compromise.html
- https://github.com/fireeye/sunburst_countermeasures
- http://hackdig.com/12/hack-227727.htm
- https://www.fireeye.com/blog/threat-research/2020/12/evasive-attacker-leverages-solarwinds-supply-chain-compromises-with-sunburst-backdoor.html
- https://documentation.solarwinds.com/en/Success_Center/orionplatform/content/core-secure-configuration.htm