Updated: July 13, 2021
Note: Kaseya has released a patch for this critical vulnerability which is described here. If you use the Kaseya VSA product, please follow these directions before turning the server back on.
The Cybersecurity and Infrastructure Security Agency (CISA) has issued an alert about a recent ransomware attack against Kaseya VSA (Virtual System Administrator).
Netsurion’s EventTracker SOC recommends that you validate and ensure that the mitigation steps are followed in case Kaseya VSA components are part of your organization.
Ransomware Attack Through Kaseya VSA
A.N. Ananth, president and chief strategy officer, breaks down what exactly happened with the Kaseya VSA ransomware attack, how it compares to the SolarWinds supply chain attack, what the ramifications are for you and future attacks, and lessons learned for managed service providers (MSPs) and in-house cybersecurity teams.
Description
Kaseya announced a notification about an attack against Remote Monitoring and Management tool VSA for on-premises customers.
Determined Impact
- Attacker turns off administrative access to the VSA
- Ransomware-based threat actors are actively exploiting Kaseya VSA
Mitigations/ Workarounds
- The Kaseya team is in the process of investigating the root cause of the incident with an abundance of caution
- Kaseya recommends to IMMEDIATELY shut down your VSA server until you receive further notice from Kaseya
- To validate the existence of known malicious files, on-premises VSA customers can Extract and Run Kaseya’s self-assessment PowerShell script on both the VSA server and associated endpoints
- KaseyaVSADetectionTool.ps1 – This script will help to validate the existence of potentially malicious files on the Kaseya VSA server
- KaseyaEndpointDetectionTool.ps1 – This script will help to validate the existence of potentially malicious files on your endpoint Workstation/Servers
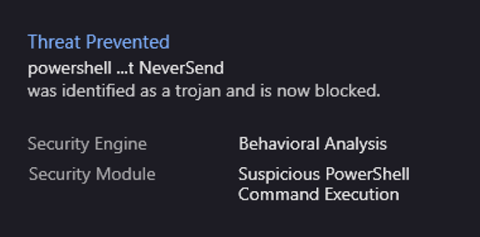
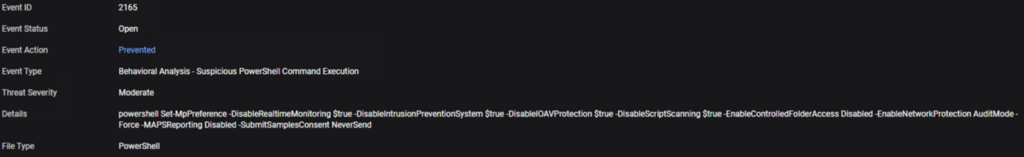
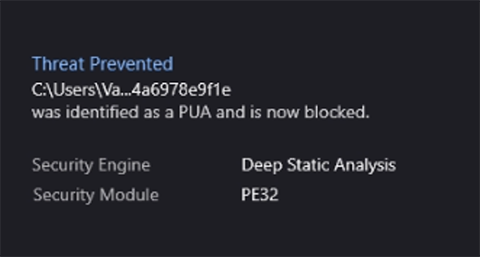
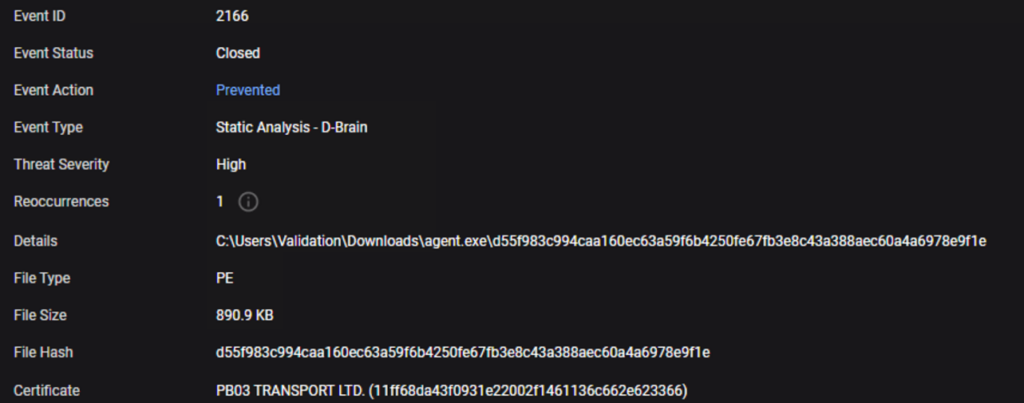
As the screenshots below indicate, this malicious behavior was prevented for EventTracker Endpoint Security customers. So, those customers have time to shut down their VSA servers when ready. However, if you do not have EventTracker Endpoint Security coverage, you must act now to shut down your VSA servers, as you are not protected.
As an additional point of validation, Netsurion highly recommends reviewing and removing any exclusions which have been put in place surrounding Kaseya directories, including the common working directory of C:\kworking which is recommended by Kaseya to be excluded from anti-virus (AV) vendors.
We are continuing to monitor attack patterns related to the Kaseya VSA supply chain attack and will resume IOC updates in the EventTracker Threat Center.
Indicators of Compromise (IOCs)
| IOC Type | Value |
|---|---|
| MD5 | 561cffbaba71a6e8cc1cdceda990ead4 |
| a47cf00aedf769d60d58bfe00c0b5421 | |
| 7ea501911850a077cf0f9fe6a7518859 | |
| 10ec4c5b19b88a5e1b7bf1e3a9b43c12 | |
| 0299e3c2536543885860c7b61e1efc3f | |
| 835f242dde220cc76ee5544119562268 | |
| 5a97a50e45e64db41049fd88a75f2dd2 | |
| be6c46239e9c753de227bf1f3428e271 | |
| 18786bfac1be0ddf23ff94c029ca4d63 | |
| 849fb558745e4089a8232312594b21d2 | |
| 4a91cb0705539e1d09108c60f991ffcf | |
| 7d1807850275485397ce2bb218eff159 | |
| 040818b1b3c9b1bf8245f5bcb4eebbbc | |
| a560890b8af60b9824c73be74ef24a46 | |
| a9f731de650ee1ba0ef91e1386ac2dad | |
| 0fb09ae7a5ef2c1c9fe189fb3d2e3507 | |
| 10a09a96cb6a005bccf75cd8221f8599 | |
| ed610aaba5a4ef5c2fe5ce4a7662709f | |
| Involved Processes | C:\Windows\System32\certutil.exe |
| C:\Windows\cert.exe | |
| C:\kworking\agent.crt | |
| Process Command Lines | C:\WINDOWS\system32\cmd.exe” /c ping 127.0.0.1 -n 4979 > nul |
| C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe Set-MpPreference -DisableRealtimeMonitoring $true -DisableIntrusionPreventionSystem $true -DisableIOAVProtection $true -DisableScriptScanning $true -EnableControlledFolderAccess Disabled -EnableNetworkProtection AuditMode -Force -MAPSReporting Disabled -SubmitSamplesConsent NeverSend & copy /Y | |
| C:\Windows\cert.exe & echo %RANDOM% | |
| C:\Windows\cert.exe & C:\Windows\cert.exe -decode C:\kworking\agent.crt | |
| C:\kworking\agent.exe & del /q /f | |
| C:\Windows\cert.exe & c:\kworking\agent.exe | |
| Registry Keys | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\BlackLivesMatter |
| Domains | ncuccr.org |
| 1team.es | |
| 4net.guru | |
| 35-40konkatsu.net | |
| 123vrachi.ru | |
| 4youbeautysalon.com | |
| 12starhd.online | |
| 101gowrie.com | |
| 8449nohate.org | |
| 1kbk.com.ua | |
| 365questions.org | |
| 321play.com.hk | |
| candyhouseusa.com | |
| andersongilmour.co.uk | |
| facettenreich27.de | |
| blgr.be | |
| fannmedias.com | |
| southeasternacademyofprosthodontics.org | |
| filmstreamingvfcomplet.be | |
| smartypractice.com | |
| tanzschule-kieber.de | |
| iqbalscientific.com | |
| pasvenska.se | |
| cursosgratuitosnainternet.com | |
| bierensgebakkramen.nl | |
| c2e-poitiers.com | |
| gonzalezfornes.es | |
| tonelektro.nl | |
| milestoneshows.com | |
| blossombeyond50.com | |
| thomasvicino.com | |
| kaotikkustomz.com | |
| mindpackstudios.com | |
| faroairporttransfers.net | |
| daklesa.de | |
| bxdf.info | |
| simoneblum.de | |
| gmto.fr | |
| cerebralforce.net | |
| myhostcloud.com | |
| fotoscondron.com | |
| sw1m.ru | |
| homng.net |
FAQs
- What is VSA?
Virtual System Administrator (VSA) is the Remote Monitoring and Management (RMM) tool from Kaseya used to automate software patch management and vulnerability management. - How do I know if I have it?
Refer to your organization’s asset inventory and validate whether you are using the on-premises Kaseya VSA tool for Remote Monitoring and Management. - How to identify the malicious file?
If you are using the on-premises Kaseya VSA component, Extract and Run the self-assessment PowerShell script on both the VSA server and associated endpoints. - How to run the self-assessment tool?
Watch the installation walk through on Run and follow the instructions from Instructions.pdf. - How to shut down Kaseya?
Follow the steps listed on https://helpdesk.kaseya.com.
References
- https://www.kaseya.com/products/vsa/
- https://helpdesk.kaseya.com/hc/en-gb/articles/4403440684689
- https://www.bleepingcomputer.com/news/security/revil-ransomware-hits-200-companies-in-msp-supply-chain-attack/
- https://therecord.media/revil-ransomware-executes-supply-chain-attack-via-malicious-kaseya-update/
- https://www.msspalert.com/cybersecurity-breaches-and-attacks/kaseya-rmm-cyberattack-warning/
- https://us-cert.cisa.gov/ncas/current-activity/2021/07/04/cisa-fbi-guidance-msps-and-their-customers-affected-kaseya-vsa
- https://helpdesk.kaseya.com/hc/en-gb/articles/4403440684689
- https://www.scmagazine.com/home/security-news/ransomware/kaseya-vsa-may-be-under-active-attack-recommends-shutdown/
- https://community.sophos.com/b/security-blog/posts/active-ransomware-attack-on-kaseya-customers
- https://www.scmagazine.com/home/security-news/ransomware/kaseya-announces-breach-detection-tool-in-vsa-fight/
- https://kaseya.app.box.com/s/0ysvgss7w48nxh8k1xt7fqhbcjxhas40
- Kaseya Install Guide
