Your organization’s Software-as-a-Service applications are mission critical. User productivity and effectiveness depend on SaaS apps like Salesforce, Dropbox, Workday, Slack, and more. In cooperation with SaaS providers, we restore visibility to user, application, and data behavior through audit/logging, PowerShell activity tracking, and a 24/7 SOC to detect and escalate incidents. Netsurion alerts you to application security problems and recommends mitigation steps long before a disastrous failure occurs.
Centralize Cloud Visibility and Security
Your move to the cloud expands your attack surface and necessitates a move to more advanced security. Microsoft security is just a starting point. Netsurion makes security easier by providing 24/7 monitoring, rapid alerts, comprehensive reporting, and executive dashboards.
Benefits include:
- Enhanced security coverage no matter where your data resides
- Unified view of risk with single-pane-of-glass visibility
- Faster detection of threats and malicious activity
- Expanded coverage that scales as your infrastructure grows
- Additional cost savings with a centralized approach to cybersecurity


Salesforce Integration
Most businesses use Salesforce or another CRM for daily business tasks, from sales to customer service to marketing automation. With so much data at risk, comprehensive security strategies are a must.
- Monitor: the actions performed by admin users such as user accounts added or deleted and escalation of privilege requests, PowerShell activity tracking, sign-ins from multiple geographies all with centralized reporting in the Netsurion console
- Track: user login activities to SaaS apps with geo-location for identifying compromised accounts
- Identify: suspicious login attempts and receive an alert when a first-time user login occurs from a new location or suspicious IP address
- Detect: brute force login attempts using geographic information such as countries where your organization does not operate, and unusual changes to passwords and policies
Slack Integration
Slack is a widely used collaboration hub where you and your team can work together to get things done. In Slack, work happens in channels. We can monitor the audit events in Slack Enterprise Grid. Netsurion integrates with Slack Enterprise Grid to monitor the activities on the Slack Enterprise Grid such as Channel events, File uploads, User events etc.
- Security: Login and logout events and lser privilege escalation.
- Compliance: Channel and workspace created, deleted and modified.
- Operation: Apps created, installed and uninstalled, user activity etc.
Box Integration
The Box is a cloud computing business that provides file-sharing, collaborating and other tools for working with files that are uploaded to its servers. Users can determine how their content can be shared with other users.
Netsurion helps to monitor activities such as file/folder operations, policy violations, administrator, role changes, login failures, etc. Once events are received into Netsurion, alerts and reports can be configured into Netsurion. Netsurion monitors all the Box events, some of them are given below.
- Monitoring security actions such as malicious files detected, login failure, etc.
- Monitoring operational activities such as item created, deleted, modified, etc.

Great experience using the system and working with their security team… We have the co-managed SIEM and the Netsurion SOC analysts are a great addition to our security team. The integrations from third-party systems help show us the full picture, from on-prem to Microsoft 365.
Shield Cloud Environments from Hackers
Organizations now rely on the cloud for primary means of communicating with employees, suppliers, and customers. Netsurion helps safeguard the flow of email to keep your “always on” organization up and running.
- Audit administrator actors, including mailbox creation and mailbox deletion
- Monitor changes to Microsoft 365 Exchange policies that might result in a security gap such as malware, spam, and spoofed emails
- Identify users accessing mailbox folders, purging deleted items, and accessing other mailbox accounts
- Trace emails to track the organization’s mail flow
- Monitor PowerShell activity tracking
Do you use Exchange Server on-premises? Read the HAFNIUM Security Alert now.
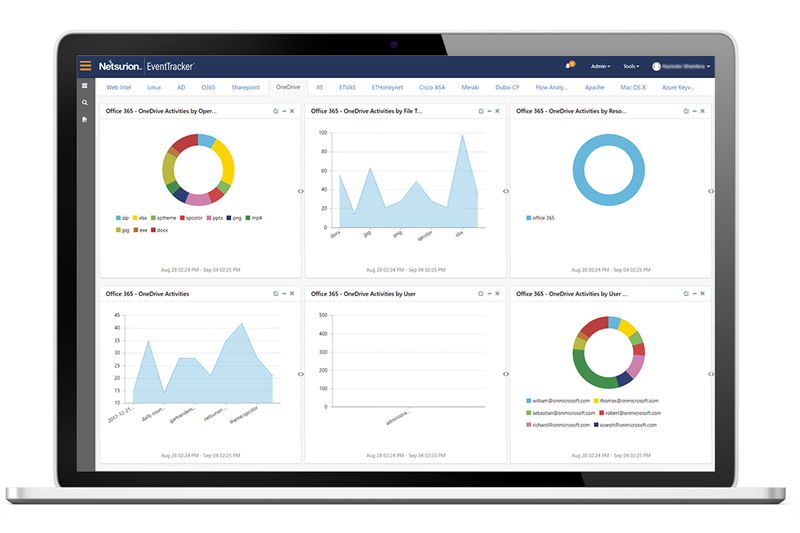
Protect Sensitive Data Stored in the Cloud
A 24/7 SOC to watch for and escalate alerts is crucial to detect suspicious activities that may signal information leakage or a costly data breach:
- Monitor application administrator actions such as site added, deleted or modified
- Generate comprehensive reports for hands-on users and executives
Success Stories
Our security operations center and AI-driven threat protection platform review billions of logs daily to defend customers from advanced threats. Here are just a few real-world examples.