What is SIEM?
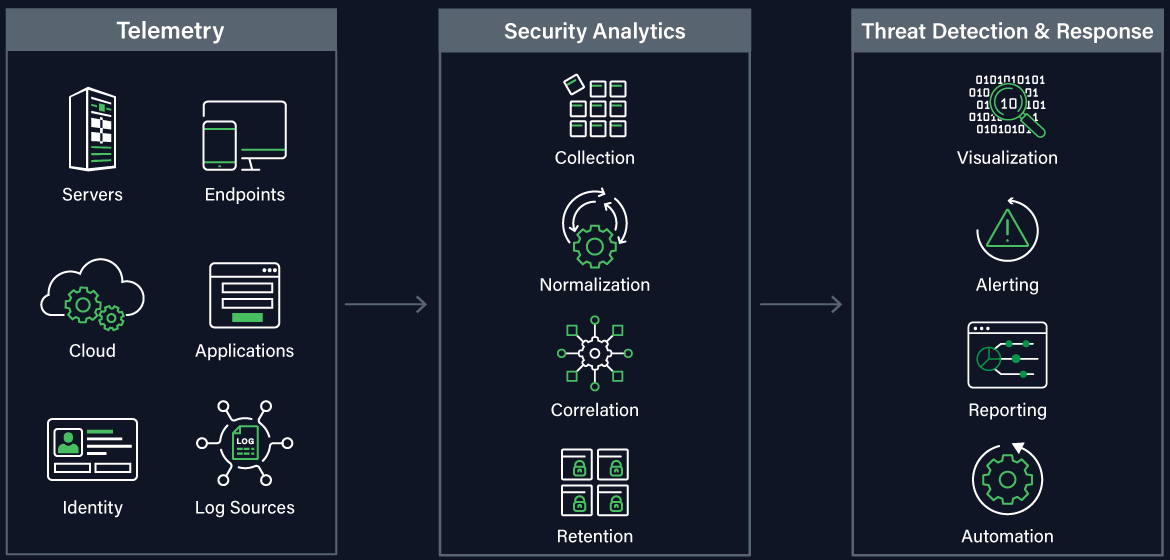
SIEM (Security Information & Event Management) technology is a critical component of XDR (Extended Detection & Response) capabilities. SIEM ingests event log data from a wide range of telemetry sources across your IT assets, analyzes and correlates against threat intelligence to identify potential threats, and ultimately triggers alerts and potentially automated responses. SIEM includes log management for compliance use cases and provides deep security analytics. SIEM technology has evolved over the years to keep pace with the cyberthreat landscape. As a result, there is a broad range of SIEM solutions available that offer very different levels of functionality including UEBA (User and Entity Behavior Analytics) and security orchestration and automation.
SIEM at a Glance
As your IT infrastructure expands, your network perimeter dissipates, and your reliance on cloud environments and third-party applications grows, SIEM becomes more and more important for cyber threat detection and vulnerability management.
Why Managed SIEM?
As powerful and foundational that SIEM technology is to your security operations (SecOps), it is also complex to implement optimally and continuously maintain for expected business outcomes. It is not an uncommon in cybersecurity for organizations to have attempted to implement SIEM in-house only to fail due to the lack of appropriate expertise and/or the lack of resource bandwidth. This challenge has led organizations to seek Managed SIEM – a managed service that includes a team of experts known as a Security Operations Center (SOC) that will configure, deploy and maintain the SIEM technology as well as be the primary user of the system to monitor, detect, and respond to cyber threats. Managed SIEM has proven to be much more effective and affordable than licensing SIEM technology and staffing a SOC in-house to drive it. Managed SIEM encompasses the core costs for staffing and tooling a 24×7 SOC.
How Netsurion Managed SIEM Works
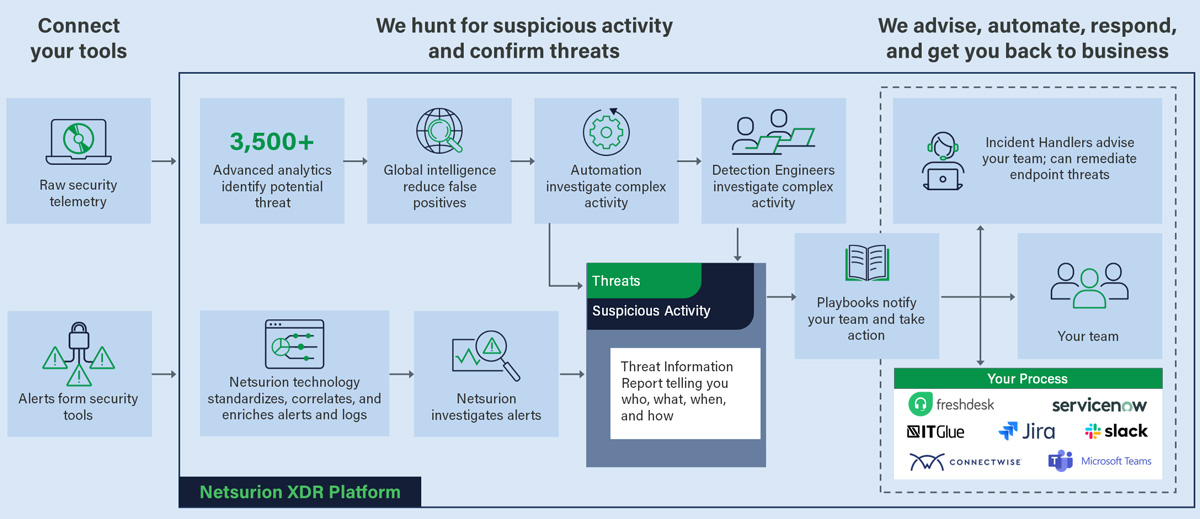
Netsurion’s Open XDR is built upon a robust SIEM platform with wide data source integration, deep threat detection, and all of the expertise to configure, tune, and continuously maintain for optimal outcomes.
Wide Coverage and Deep Detection
Netsurion’s SIEM sees your entire attack surface – ingesting, normalizing, and correlating security telemetry from thousands of data sources. Keep your existing tools to accelerate tech stack ROI across your endpoints, networks, servers, cloud, and SaaS applications. Boosted by MITRE ATT&CK™ mapping and UEBA-focused machine learning, we log billions of events to block known threats and alert you to real attacks while minimizing false positives.


Embedded Threat Intelligence
In addition to incredibly wide support for your attack surface telemetry, Netsurion’s SIEM capabilities includes Netsurion Threat Center, our threat intelligence platform. Threat Center provides additional context and correlation between seemingly unrelated security events resulting in faster identification of Indicators of Attack (IoAs).
Netsurion ingests over 30 open-source intelligence (OSINT) feeds and uses the STIX/TAXII framework to automate the process of threat detection, analysis, and response.
Streamline Compliance Management
Netsurion Managed SIEM helps your organization reduce risk and improve operational efficiency by using SIEM to automate the steps required by various industry regulations and government mandates. Keeping up with the changes in regulations and additions of new mandates can be time consuming, tedious, and if not done correctly – a dangerous liability for your organization.
Simplify your day-to-day security operations with our combined SIEM, attack surface management, and 24×7 Security Operations Center (SOC) approach. Organizations can secure the environment, establish a baseline of good behavior, track user activity, and alert on potential violations. Netsurion generates audit-ready reports to help with PCI DSS, HIPAA, ISO 27001, NIST 800-171, DoD, RMF, GDPR, and other compliance requirements.

Related Resources
Talk to a Cybersecurity Advisor
Looking to optimize your cybersecurity posture with Managed SIEM? Choosing the right partner is crucial. Talk to a Cybersecurity Advisor to see if we’re a fit