MFT Server Exploit Intercepted in Mid-Air
The Network: An American cargo airline with more than 650 monitored network systems across multiple locations.
The Expectation: By performing regular vulnerability assessments, routinely patching public-facing assets, maintaining them in a DMZ (demilitarized zone) separate from untrusted networks, the Vulnerability Management team within the airline will prevent a vulnerability from being exploited.
The Catch: Netsurion’s Open XDR platform alerted the Netsurion SOC to nefarious domain enumeration activities including domain admin user listing, share access, service collections, and password dump file extraction from the Security Accounts Manager (SAM) in Microsoft Windows.
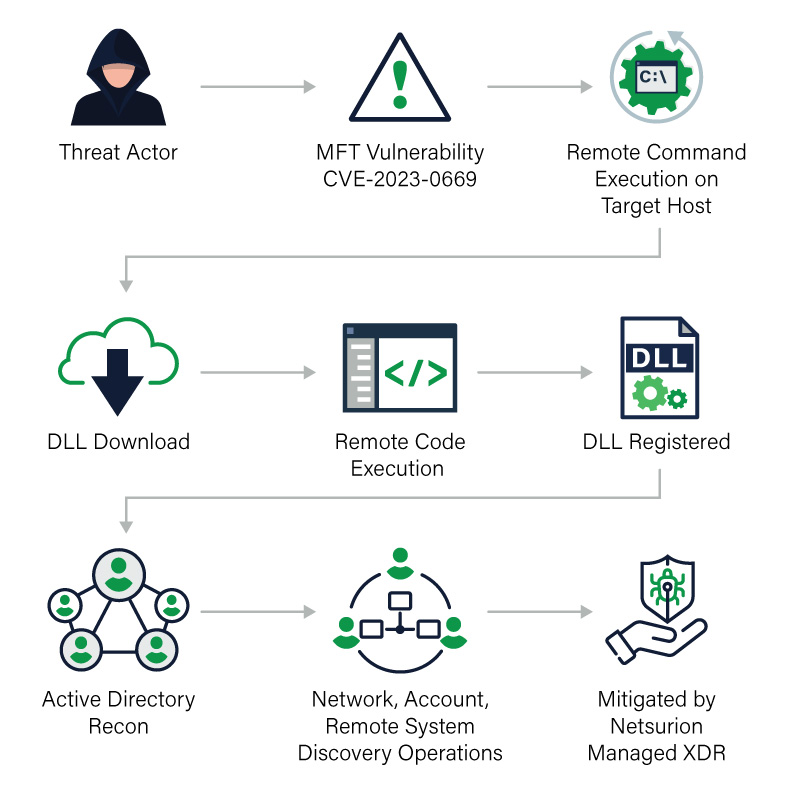
The Find: After further analysis, our SOC found suspicious activities initiated from the airline’s MFT (managed file transfer) server that successfully gained access to high-privileged accounts and conducted domain level enumeration activities. The SOC analyzed the events, performed triage, and guided the airline through remediation.
With MITRE ATT&CK framework-based forensics integrated into the Netsurion Open XDR console, our SOC was able to immediately identify the infected systems and monitor for similar patterns across the airline’s network.
Adversary Techniques Detected
| Execution | Discovery | Command and Control |
|---|---|---|
The Netsurion SOC suspected the threats actors likely have identified the vulnerable MFT server components using open-source scan engines like Shodan.io.
The Fix: Netsurion prevented a severe compromise by detecting the malicious patterns on the “patient zero” machine and guided the airline IT staff through containment and incident remediation steps.
Netsurion’s SOC identified both the domain enumeration attempts, exploit tool usage, and password dump file extractions. Specifically, the key alerts were:
- A Suspicious exploit tool detected.
- A Suspicious exploit attempt detected.
- Active Directory Enumeration attempt detected.
Our SOC arranged an incident response call to explain the postmortem analysis and suggested best practices. Netsurion’s quick response ensured the airline was able to thwart the threat actor before damage could be done.
It was found that the vulnerable GoAnywhere MFT application was exploited and access to the administration interface was not properly restricted.
The Lesson: Organizations needs to scan and patch routinely and quickly. Emergency patches needs to be applied immediately to avoid exploits. Vulnerability scans must be done consistently and be part of a full-fledged vulnerability management program to prevent adversaries from exploiting unpatched systems and sneaking in without a trace. Nonetheless, threat detection and incident response activities must be operated 24x7x365 to catch active threats and incidents of compromise (IOCs) such as this.
Some preventive measures to avoid and incident like this are:
- Perform vulnerability assessment and patching activity frequently and consistently.
- Deploy public-facing components within a DMZ.
- Restrict access to administration interfaces for specific IP address.
- Disable network discovery options by default.
Related Resources
- https://nvd.nist.gov/vuln/detail/CVE-2023-0669
- https://latesthackingnews.com/2023/02/07/emergency-patch-released-for-goanywhere-mft-zero-day-vulnerability/
- https://frycos.github.io/vulns4free/2023/02/06/goanywhere-forgotten.html
- https://thehackernews.com/2023/02/cisa-warns-of-active-attacks-exploiting.html