Unpatched Server Exploit Puts International Franchise System at Risk
The Network: An international franchise system with approximately 200 systems protected by Netsurion.
The Expectation: By performing regular vulnerability assessments, routinely patching public-facing assets, maintaining them in a DMZ (demilitarized zone) separate from untrusted networks, the Vulnerability Management team within the company will prevent a vulnerability from being exploited.
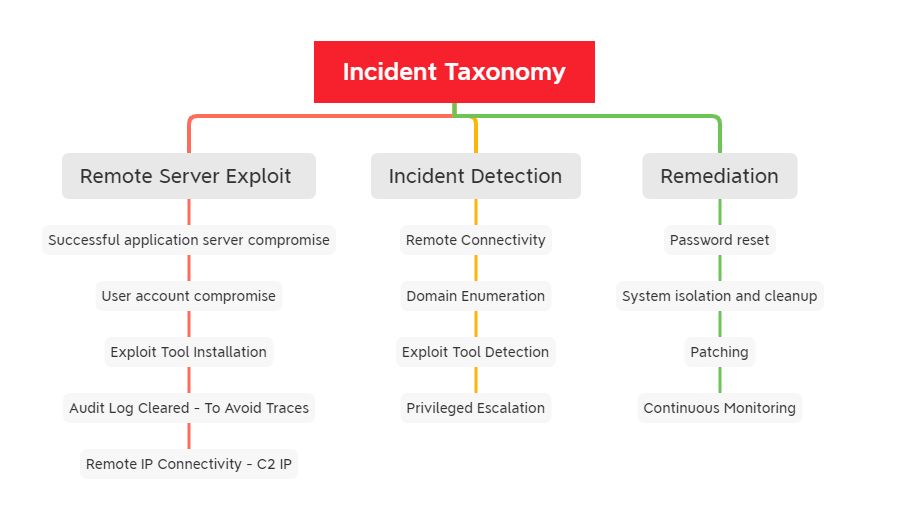
The Catch: Netsurion’s Open XDR platform alerted the Netsurion SOC to nefarious domain enumeration activities along with exploit tool usage on the company’s primary business application server that was not patched and was therefore prone to exploits and attacks.
The Find: After further analysis, Netsurion’s SOC found suspicious activities initiated from the company’s public-facing business application server, where the adversary gained access to high-privileged accounts and conducted domain level enumeration activities using the popular exploitation tool, Mimikatz. The SOC quickly detected this and informed the customer.
The analysis also discovered that the targeted server was not patched to fix CVE-2021-21551. There were also traces of a “Pass the Hash” attack using built-in Windows tools, remote exploitation tools and remote connections.
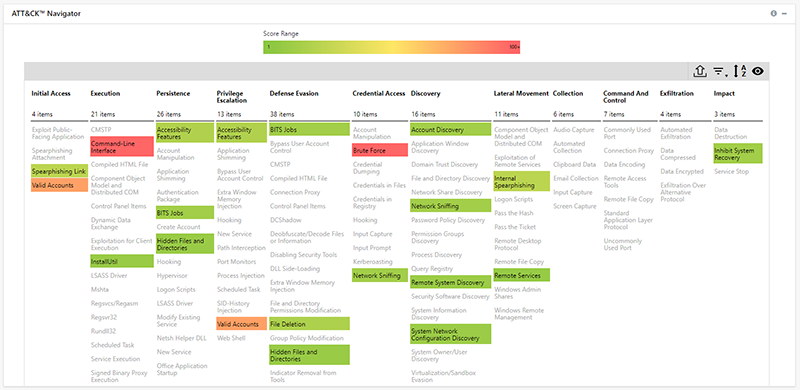
Leveraging the MITRE ATT&CK framework integrated within the Netsurion Open XDR console and Priority-1 alerting, our SOC was able to immediately identify the infected systems and monitor for similar patterns across the company’s network.
P-1 Alerts
- Netsurion: New Windows network process activity
- Netsurion: Suspicious exploit tool detected
- Windows: Audit log cleared
Adversary Techniques Detected
The Netsurion SOC suspected the threat actors likely identified the vulnerable application server components using remote exploitation as the server could be connected to externally.
The Fix: Netsurion prevented a severe compromise that would have included global business downtime and additional IT remediation time by detecting the malicious patterns on the “patient zero” machine and guided the fitness company through containment and incident remediation steps.
Netsurion security analysts identified the domain enumeration attempts, exploit tool usage, and password dump file extractions.
Our SOC arranged an incident response call to explain the postmortem analysis and suggested best practices. Netsurion’s quick response ensured the company was able to thwart the threat actor before damage could be done.
It was found that the vulnerable application was exploited and access to the administration interface was not properly restricted. CVE-2021-21551 was the active critical vulnerability exposure that had to be patched in the server.
The Lesson: Organizations need to scan and patch routinely and quickly. Emergency patches need to be applied immediately to avoid exploits. Vulnerability scans must be done consistently and be part of a full-fledged vulnerability management program to prevent adversaries from exploiting unpatched systems and sneaking in without a trace. Nonetheless, threat detection and incident response activities must be operated 24x7x365 to catch active threats and incidents of compromise (IOCs) such as this.
Take preventive measures to avoid a similar incident:
- Implement a Web Application Firewall (WAF).
- Enable Multi-Factor Authentication (MFA) for all user accounts.
- Require all accounts (e.g., service account, admin accounts, and domain admin accounts) to have strong, unique passwords.
- Restrict RDP access to critical servers from specific accounts only.
- Keep all operating systems and software up to date.
- Remove unnecessary access to administrative Shared Folders.
- Use a host-based firewall to only allow connections to administrative Shares via Server Message Block (SMB) from a limited set of administrator’s machines.
- Identify your exposed assets – anything on the public internet – and restrict access to required services only.
- Implement network segmentation.
- Close unused ports and disable unused protocols.
- Remove inactive user accounts.
- Implement time-based access for accounts set at the admin level and higher.
- Use administrator accounts only when necessary.
References:
https://attack.mitre.org/software/S0002/
https://www.cvedetails.com/cve/CVE-2021-21551/
https://github.com/waldo-irc/CVE-2021-21551