Ransomware Detected & Blocked in Business Services Firm
The Network: A business services firm with over 1,110 consultants across 4 locations that advises end-clients nationwide. Their IT team is supplemented by Netsurion’s Open XDR platform and cybersecurity experts to provide comprehensive threat detection and response.
The Expectation: Protecting business data and end clients is vital given that cyber criminals who steal personally identifiable information (PII), intellectual property, or financial data jeopardize the reputation and trust given to the long-standing organization. Netsurion’s Open XDR platform and 24×7 SOC combine to predict, prevent, detect, and respond to advanced cyber threats against the company with continuous monitoring and guided remediation. Endpoint security also protects all systems and applications with Intrusion Detection System (IDS) and Vulnerability Management to identify gaps before cyber criminals can exploit them.
The Catch: Netsurion’s Managed XDR detected suspicious process execution on several systems and the built-in Application Control capability prevented several ransomware processes on multiple systems. Further, the SOC also detected network connection attempts to external Command & Control (C&C) servers by several of the business services workstations. Cyber criminals use C&C servers for ransomware campaign management and to receive stolen data. This holistic detection by Netsurion’s SOC analysts enabled the business services organization to avoid data compromise.
Ransomware employs encryption to hold a victim’s information for hostage. A user or organization’s critical data is encrypted so that they cannot access files, databases, or applications. A ransom is then demanded to provide access. Ransomware is often designed to spread across a network by targeting databases and file servers, which can then quickly paralyze an entire organization.
The Find: The Netsurion SOC detected a ransomware infection after analyzing the telemetry ingested by Netsurion’s Open XDR platform with its single-pane-of-glass visibility.
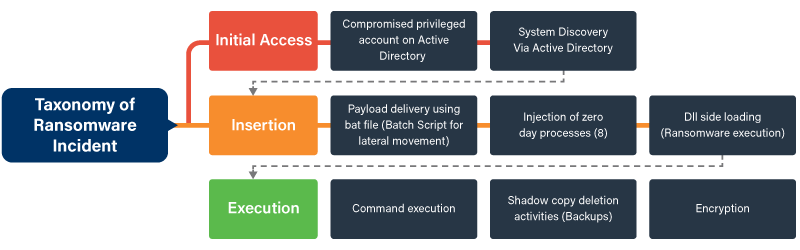
Several of the many MITRE ATT&CK® techniques observed included:
| ATT&CK ID | Tactic | Technique |
|---|---|---|
| T1059 | Execution | .bat file executions |
| T1073 | Defense evasion and execution | psExec.exe, F***GPO.exe, VMwareExferlogs.exe, File deletion, DLL side loading |
| T1082 | Discovery | System information discovery |
| T1485 | Impact | Shadow copy deletion |
The Netsurion team observed Command Line Interface (CLI) executions starting from a domain server spreading across the affected hosts and random.exe file executions loading “lilis.sys” which in turn loads “RTcore64.sys”. This file was an MSI driver with CVE-2019-16098 (privileged escalation exploit vulnerability), the likely reason for the compromise.
The Netsurion SOC team also detected .exe file executions from directory C:\windows\Temp with random alphanumeric named files and Shadow Copy Deletion on the impacted hosts, which is a clear pattern of a ransomware anomaly.
Psexec.exe and f***GPO.exe file executions were also detected on domain server in the compromised account profile path C:\Users\accountname\Desktop\F***GPO.exe and C:\Users\accountname\Desktop\PsExec.exe.
Incident Timeline:
- At 1:09 a.m. EST, Netsurion Endpoint Security prevented the threats on the managed devices of the business services organization.
- At 1:15 a.m. EST, the Netsurion SOC quickly detected the backup deletion activities.
- At 2:00 a.m. EST, the SOC updated the Indicators of Compromise (IoCs) on Netsurion Threat Center, ensuring that all Netsurion customers and partners can benefit from the actionable threat intelligence.
- At 3:00 a.m. EST, the SOC analysts identified bad MD5 hash values to managed devices for process termination.
- At 4:02 a.m. EST, Netsurion created a real-time alert to monitor similar activities.
- At 9:00 a.m. EST, the SOC updated Endpoint Protection policies to “prevent state” for newly-deployed endpoint agents.
- At 9:03 a.m. EST, Customer blocked the suspicious IP address.
- At 9:15 a.m. EST, Customer changed the password of the SA account and performed clean-up activities following Netsurion-provided remediation guidelines.
- Total remediation time: a time to Detect & Respond of less than 24 hours.
The Fix: Guided remediation from the Netsurion SOC included:
- Ensure all devices such as Netsurion Endpoint Security workstations are reporting and active
- Check for Netlogon activities and the presence of any vulnerabilities
- Apply updates and patches across all systems, especially driver updates
- Harden Microsoft 365 such as:
- Restrict downloads of unauthorized applications
- Limit access to crucial users only (role-based access control)
- Enhance user education regarding phishing emails and application download and installation
- Consider performing a policy assessment per:
- Ensure that the hardening of the system is up to date and all systems are patched accordingly
The Netsurion SOC also provided recommendations on the reimaging of the infected servers and workstations. Additional best practices and guided remediation advice were provided regarding security controls as well as cybersecurity awareness and training for users.
The Lesson: Legacy anti-virus (AV) solutions are often bypassed by financially motivated attackers. Regular patching with the latest updates should be implemented and validated regularly. Better user access controls and Multi-Factor Authentication (MFA) is highly recommended to protect privileged accounts like those for sys admins. Finally, comprehensive 24/7 monitoring by cybersecurity experts can detect and block threats before data is stolen or the company’s reputation damaged.
| Category | Type | Value |
|---|---|---|
| Application | Executable | VY887.exe |
| 9OGS9.exe | ||
| L7TY7.exe | ||
| 6IP79.exe | ||
| SC62U.exe | ||
| 4OCI5.exe | ||
| F***GPO.exe | ||
| 3PUGY.exe | ||
| Payload | MD5 | MD5 |
| d2cc8269b9dc92da0f51477d341c307d | ||
| 3959f7142f244abf8a6807c9b5f5a42e | ||
| 6993eb108108739b31a8e9d76618a85f | ||
| DAF48639F476BF8B6164D58123253660 | ||
| 66DCA82AAE326756DD69D76A10824C55 | ||
| Other Creator Hash values | ||
| 10fdbe1525df2e793ee211c5e741d0c0 | ||
| e27436fcdce62528360754b883465bc1 | ||
| a7d4e2c269301bea243676ed56f8b4ff | ||
| 5c4f90e4f60efbb8f5fab49777ac701d | ||
| 385a7035b3da723b4ffefc4050085fdd | ||
| d671e381500e76d444755d4d690ea1a0 | ||
| 6f8489396f9de70be507f1a9babfdf21 | ||
| 586f24d606361a8ee7f26e31c6f7f0ca | ||
| 69b860d6dad6defd6c2aa5172e284fdb | ||
| 946a5ef8447b5212f66978dec1673a6f | ||
| 4f428d58939450f5a3747d96397a0825 | ||
| 589dd5af13134f0ac7ee846c0c46d86d | ||
| 79745df4848430abf5767d7d08c56b6f | ||
| dedb97e50df5fd70af3e59528f1b6a6d | ||
| 6465e1159b1379fe4815c56ddebf3473 | ||
| bc28471e2faf0debeff6fa3b9fa97229 | ||
| bcebd7b67acbaa37927a9f326179194e | ||
| IP Address | IPv4 | 45[.]32[.]101[.]191 |
| Domain | Domain | Vultr[.]com |